Breaking Down Audit Inefficiencies: Lessons from 36,000 Audits
For most compliance managers and IT security leaders, audit season follows a familiar pattern: repeated evidence requests, gathering documentation from scratch, and losing critical context with each new cycle. Most teams spend a disproportionate amount of time managing audit logistics, taking them away from other critical components of compliance. In fact, two-thirds of organizations spend more than three months preparing for audits — putting a heavy strain on both teams and productivity. These challenges aren’t a sign of a poorly run program. They’re a reflection of how most audit processes were designed before modern compliance demands existed.
After completing over 36,000 audits, A-LIGN has identified the recurring patterns that cause even the strongest compliance programs to stall. One of the biggest sources of audit pain isn’t gaps in security controls — it’s a broken process. Inefficient tools, scattered communication, and time-consuming manual work slow progress for both auditors and clients.
Below we break down the key reasons compliance programs routinely falter and how to address them.
The most commons ways compliance programs break down
Even the most mature organizations struggle with the operational side of compliance. These are five common patterns that frequently contribute to audit inefficiency.
The evidence management trap
Evidence management often starts with a well-organized folder or master spreadsheet. But as the audit progresses, these tools quickly become cluttered with colored cells, conflicting versions, and broken links. Without a centralized, integrated system, evidence becomes scattered and difficult to manage. This leads to submitting the same files multiple times when auditors can’t locate them, or wasting hours manually matching documents to requirements. These manual processes not only increase the risk of errors but also force skilled security professionals to spend audit season chasing files and formatting spreadsheets instead of identifying and closing actual security gaps.
The “starting from scratch” cycle
The annual audit cycle often brings a loss of important context from previous reviews. Months are spent providing information and guiding auditors through complex environments. Once the report is delivered, attention shifts to new priorities, and the background that informed key decisions is often forgotten.
A year later, the entire process begins again. Notes explaining decisions around specific controls are lost, the same questions are asked, and identical baseline evidence is gathered. Without the ability to reuse past data, every audit cycle feels like starting from scratch.
Multi-framework redundancy
As organizations grow, so do their compliance obligations. Many start with SOC 2, then add ISO 27001, and later take on frameworks like HITRUST or HIPAA. Despite significant overlap between these frameworks, audits are often treated as completely separate projects and on different cycles. The same policy documents are collected and presented multiple times for different auditors or standards. Without tools to map and reuse evidence across requirements, teams duplicate work, strain subject matter experts, and drive up the overall cost and complexity of compliance.
Late gap discovery
Few things stall an audit faster than a critical gap discovered right before or during fieldwork. Often, materials appear complete until auditors review evidence and find missing details or documentation that doesn’tfully meet requirements. This triggers a last-minute scramble, pulling resources away from planned work and interrupting timelines when accuracy matters most. Identifying these gaps only after fieldwork begins not only delays the process but also increases stress and operational risk.
Stakeholder coordination breakdown
Compliance doesn’t happen in isolation. Engineering, HR, legal, and operations teams all play critical roles in providing required data and documentation.
Audits managed through scattered email threads and chat messages often suffer from a breakdown in stakeholder coordination. Internal teams experience audit fatigue from repeatedly supplying the same data. Missed messages and forgotten follow-ups slow project progress. Without a centralized platform to track requests and communications, achieving consistent alignment among all parties becomes extremely difficult.
A smarter approach to audit management
Thorough inspection and validation are critical to ensuring audit quality. The real challenge lies in eliminating the avoidable friction that slows teams down.
Expecting compliance professionals to manage complex, multi-framework audits with spreadsheets only adds to their frustrations. Software alone cannot resolve process issues, and expertise alone cannot scale without the right tools. Audit expertise and technology must work together within a unified system.
This realization shaped the development of A-SCEND, A-LIGN’s proprietary audit management platform built from the ground up. A-SCEND centralizes evidence, connects stakeholders, and enables historical data to be reused year after year. By unifying people, processes, and technology in one platform, it reduces redundant requests and maintains alignment from preparation through to the final report.
Audit season no longer needs to be a taxing cycle of starting over. By addressing these recurring challenges and adopting a more integrated, tech-enabled approach, organizations can streamline the process and focus on strengthening their compliance programs.
Understanding GSA’s Updated CUI Security Requirements for Contractors
On January 5, 2026, the U.S. General Services Administration (GSA) released Revision 1 of its IT Security Procedural Guide. The update outlines how Controlled Unclassified Information (CUI) must be protected when it resides in nonfederal systems operated by contractors.
While the document is framed as procedural guidance, it introduces a more defined process for how contractors demonstrate compliance and how GSA evaluates that posture. It also marks a shift away from self-attestation of compliance to NIST 800-171 and into a model involving third party assessment.
A more structured approach to CUI protection
The updated guide establishes a formal process for protecting CUI in contractor-owned systems. This includes expectations around documentation, assessment, and review before a system is approved to handle CUI in support of GSA work.
Contractors may be required to:
- Develop and maintain formal documentation, including a System Security and Privacy Plan (SSPP) and Plan of Action and Milestones (POA&M)
- Undergo third-party assessment of their security controls
- Obtain GSA approval prior to performing work involving CUI
This represents a shift toward a more standardized and reviewable approach to compliance, rather than relying solely on internal attestation.
The five phases of GSA’s CUI approval process
The guide organizes the process into five phases that contractors should understand before handling CUI in nonfederal systems:
- Prepare – Identify whether CUI will be stored, processed, or transmitted in contractor systems, and begin defining the system boundary.
- Document – Develop required materials such as the SSPP and POA&M, and related security documentation.
- Assess – Complete a third-party assessment to evaluate whether applicable security requirements have been implemented.
- Authorize – Submit required materials for GSA review and obtain approval before the system is used to handle CUI.
- Monitor – Maintain the approved security posture over time through ongoing monitoring, updates, and annual reviews.
This structure is important because it shows that GSA is not only asking contractors to implement controls. It is also defining a process for how those controls are documented, reviewed, approved, and maintained.
Alignment to NIST SP 800-171 Revision 3
One notable element of the update is GSA’s alignment to NIST SP 800-171 Revision 3.
Many organizations are still aligned to Revision 2, which remains the current baseline for programs like CMMC. As a result, contractors may need to evaluate how their existing controls and documentation map to the newer revision when working with GSA.
Requirements that cannot be deferred
The guide also identifies certain requirements that must be fully implemented before approval is granted.
These are sometimes referred to as “showstoppers,” meaning they cannot be addressed through a POA&M and must be in place as part of the initial review. This reinforces the importance of understanding which controls require full implementation upfront versus those that can be remediated over time.
Relationship to other frameworks
Although there is overlap with other federal security frameworks, such as FedRAMP and CMMC, the GSA process is distinct.
Organizations that have already invested in these frameworks may have a strong foundation, but they should not assume full alignment without validating against GSA’s specific expectations and approval process.Even contractors with mature compliance programs may find gaps when mapping their posture against NIST SP 800-171 Revision 3, navigating the five-phase approval process, or identifying controls that must be fully implemented upfront rather than remediated over time.
Contractors that aren’t prepared risk losing bids or facing delays on work involving CUI.
Key takeaways for contractors
For contractors supporting GSA or pursuing opportunities that involve CUI, the updated guide introduces a more formalized path to demonstrating compliance.
At a practical level, this includes:
- Understanding where CUI exists within your systems
- Evaluating alignment to NIST SP 800-171 Revision 3
- Preparing documentation that reflects your current security posture
- Planning for third-party assessment and GSA review
Taken together, these updates reflect a more structured approach to how CUI protections are implemented and validated within the GSA ecosystem.
How A-LIGN can help
As both a CMMC C3PAO and FedRAMP 3PAO, A-LIGN has the assessor capabilities to help contractors navigate overlapping and evolving federal requirements. We help clients understand where their existing investments apply, where gaps exist, and what a realistic path to GSA approval looks like.
Reach out today to evaluate your readiness for GSA’s updated CUI requirements.
The Real Cost of a Rejected Report
Compliance can be costly – and not just financially. It’s about building trust with your customers and demonstrating the strength of your security posture, which are vital to your business. Cutting corners on the building blocks of your compliance program could cost you more than the price of a new report; it could cost you your reputation.
Read on to learn about the real cost of a rejected report and why the budget option might cost you in the long run.
Report rejection is a reality
Low-cost audit providers look attractive, until a customer rejects your report.
According to the 2026 Compliance Benchmark Report, more than half of respondents have had a vendor or prospect reject a report.
According to a market survey of more than 500 information security, governance, and compliance leaders in the U.S. and Europe, 24% of enterprises (1,000-5,000 full-time employees) have rejected a report and 48% of strategic organizations (more than 5,000 full-time employees) have rejected a report. The stakes are high and organizations must maintain lofty expectations to protect their compliance strategy.
Why do reports get rejected?
Report rejection is more common than you’d think as organizations look to protect their reputation and remain competitive. Common reasons for rejected reports include:
- Incomplete or missing documentation
- Insufficient testing of controls
- Lack of additional findings
- Report was too templated and lacked relevant and appropriate insights
- Lack of trust in auditor reputation
The cost of a rejected report
It’s not just bruised egos; there are real financial and time costs to a rejected report. Each report rejection burns a significant amount of rework, delays, and reputational damage.
Financial costs
According to our market survey, the typical cost of a report rejection totals more than $70,000 plus over 90 days of remediation and rework required to meet expectations.
Let’s break this cost down even more:
- Cost of a rejected report: $70,000
- Typical time spent remediating: 3 months
- Remediation labor cost ($120,000 salary x 4 employees): $30,000
This brings the average hidden cost of a bad report to $100,000. An avoidable loss for a report that costs $20,000.
All of this points to one thing: quality matters. When quality slips, buyers pay twice. Once for the initial audit and again for the do-over and associated costs. The business lesson here is that saving $5,000-$10,000 on audit fees risks a six-figure hit down the line.
Reputational costs
Beyond the financial toll, a rejected report could cause your organization to lose business and lose trust from your customers.
While you may be able to spend the time and money to repeat your audit with another provider, your reputation is priceless. Repairing damage to the relationship with your customers and prospects is difficult, if not impossible.
Defining quality
Now that we understand the real cost of a rejected report and why a quality audit is worth it, let’s explore the definition of quality so your organization is backed by a high-quality final report.
The definition for quality has evolved as compliance professionals become more discerning about what makes up a quality audit report and experience. A quality audit isn’t just about the final report, but also the depth of experience and efficiency of the experience that gets you there.
According to the 2026 Compliance Benchmark Report, a high-quality audit experience is defined by:
- Auditor experience: Your auditor should have extensive experience in the audits you’re enlisting their services for. Plus, they should have plenty of happy customers who can speak to their knowledgeability.
- Use of technology: A high-quality auditor is tech-enabled, either through their own audit management software or partnerships with GRC and readiness tools. Technology ensures your audit is backed by experience and run efficiently.
- Experience with similar companies: Understanding the context of your industry and the environments your organization works in is key. An auditor’s experience with similar companies ensures your audit is up to the standards of your peers and customers.
It’s not just about how polished an auditor is, it’s about the work that goes into the report. As far as your final report goes, we recommend you evaluate final reports based on:
- Depth and specificity of each control: Thoroughly testing controls is a crucial part of the audit process. Sharing the depth and specificity of these elements demonstrates a rigorous, credible audit that will hold up.
- Relevance and customization of the report: A high-quality report will share results and recommendations that are specific to your organization, not just a cookie-cutter report.
- Demonstration of risk mitigation: Recommendations that strengthen your organization’s security posture where necessary.
Case study: Jitterbit
Jitterbit, a global leader in empowering business transformation through automation, offers a single, unified platform to integrate systems, automate workflows and build applications.
The Jitterbit team needed to demonstrate due diligence, ensure compliance, and protect sensitive data. Their previous audit provider delivered low-quality work that they couldn’t explain, forcing Jitterbit to redo work.
Their goal was a thorough SOC 2 audit, not a surface-level review.
The solution to this goal was partnering with A-LIGN to achieve SOC 1, SOC 2, ISO/IEC 27001, 42001, and other compliance initiatives. They chose A-LIGN for its auditors’ deep expertise in SOC 2 processes and controls. The A-LIGN team could clearly explain the rationale behind required controls, creating a collaborative partnership that strengthened Jitterbit’s compliance strategy.
“A-LIGN stands out as an exceptional security auditor. Their proactive approach and excellent customer service made complex compliance processes straightforward and educational. They are highly recommended for their expertise and supportive nature. A-LIGN’s deep understanding of new controls and regulations, combined with customized, clear guidance, significantly enhanced our security posture.”
– Will Au, VP of Engineering Services and Security, Jitterbit
Why A-LIGN
A-LIGN is your trusted compliance partner. We are the market leader in efficient, quality compliance.
A-LIGN provides comprehensive, industry-leading compliance expertise and is the only global provider to offer tech-enabled services that allow you to drastically reduce control overlap.
The A-LIGN difference is
- 4k+ ISO assessments
- #1 SOC 2 auditor in the world
- 6.4+ customers globally
- 96% customer satisfaction
- 400+ auditors globally
- 31k+ audits completed
Reach out today to learn how A-LIGN can help you achieve a high-quality, efficient final report.
Why Smart CISOs Consolidate Their Audits
Rick Orloff is a Fortune 1000 CISO and Strategic Advisor at A-LIGN, with over 20 years of experience at companies including Apple and eBay.
In the compliance world, we talk a lot about audit harmonization, the practice of consolidating multiple frameworks under one roof to reduce redundancy, save time, and drive efficiency. It’s a concept A-LIGN has championed for good reason: the operational and financial benefits are significant.
But when I talk about this with security leaders, the framing that actually moves people is rationalization. We’re rationalizing our audit portfolio, aligning our compliance programs, and driving a measurable ROI. Same outcome — sharper language for a technical audience.
So, let’s talk about what that looks like in practice.
The real cost of unsynchronized audits
If your organization is juggling SOC 2, ISO 27001, PCI DSS, and other frameworks individually, each with its own evidence requests, interview schedules, and internal stakeholders getting pulled in different directions, you already know the hidden tax this placeson your business, but have you actually quantified it?
At my previous company, when we consolidated and rationalized our audit portfolio with A-LIGN, we saved approximately $180,000 per year in hard costs. That alone got attention. But the number that got a lot of appreciation from engineering? We saved 12 weeks of evidence gathering.
Think about that for a moment. Twelve weeks of your engineers’ time not spent answering the same questions, pulling the same screenshots, attending the same interviews — just for a different auditor on a different framework. When I quantified that for the engineering organization and communicated what we were doing and why, the response was a genuine, heartfelt thank you. That kind of goodwill with your internal stakeholders doesn’t show up in a spreadsheet, but it’s real.
The trade-off you have to be honest about
Here’s what I told engineering when we made this change, and I want to be direct about it because it matters: there is a trade-off.
When we consolidate, we are compressing our audit window. That’s the point. But a compressed window means less runway to reschedule meetings, push back on requests, or let things slide. I was explicit with stakeholders that if we were going to do this — if I was going to go to bat and give them 12 weeks of their lives back — the ask was they must be responsive, and executives had to be accountable at the VP level.
If subject matter experts or directors went dark or started rescheduling, I didn’t chase them. I went straight to their VP. That’s not about being difficult. That’s about protecting the window we all agreed to.
The phrase “audit season” always strikes me as borrowed from the accounting world, and it doesn’t quite fit how tech organizations operate. The concept that resonates in my experience is the audit window: it opens, it runs for a certain number of weeks, and then it closes. That framing drives urgency and accountability in a way that a vague “season” simply doesn’t.
Making the case to the business
When I’ve taken audit harmonization, or rationalization, to executive teams or boards, I haven’t asked for permission. I’ve explained the decision, quantified the value, and gotten written alignment from stakeholders on their end of the bargain. Money and time savings close the conversation at the leadership level. What takes more effort is getting the organizational commitments in place before the window opens — not after.
One thing I’d encourage every security leader to consider: don’t think about compliance certifications in isolation. The right conversation to have with your Chief Revenue Officer is: “If we got that certification, would it help you close more deals? Can you put a number on it?” If sales tells you a new certification is worth $10M in ARR, the budget conversation with your CFO becomes straightforward. And if you’ve already consolidated your audit portfolio, there’s a good chance you’ve freed up the budget to pursue it without a new budget ask at all. In the past, that’s exactly what we did — we self-funded new certifications through consolidation savings.
The piece nobody tells you about
The most common questions I get when people are planning to consolidate are: “Where does this go wrong? What risks am I exposing the organization to?”
My answer, which might surprise you, is that it usually doesn’t go badly if you set the ground rules up front. The deals that go sideways are the ones where expectations weren’t set clearly before the window opened, and suddenly you’re chasing people for two weeks to get a piece of evidence. I don’t allow my team to operate that way, and I’d recommend other security leaders adopt the same posture.
What I would focus on instead is looking for opportunities to automate evidence collection. Most organizations are still gathering evidence manually. If you have a SIEM in your environment, there’s likely a configuration discussion to be had about generating audit-ready evidence artifacts automatically. That moves you from manual collection to a proactive, pre-audit posture — and it’s a conversation worth having with your audit partner before the window opens.
How to choose what comes next
Once you’ve rationalized your existing portfolio, the natural next question is: “Should we add additional certifications?” My recommendation is to use a common controls framework to run a gap analysis across certifications you don’t yet have. You may discover you’re already 80% of the way to a new certification based on controls you’re operating today. That changes the calculus entirely.
The best audit partners will surface that analysis for you proactively, and that gets at something more fundamental about what to look for in an auditor. When I’m evaluating a firm, the question I’m really asking is: “Are they a transaction company or a relationship company?”
A transactional auditor will take your existing scope, execute the work, and look for the next contract. A true partner is thinking about your business outcomes, not their revenue. That means telling you when you’re already close to a valuable certification. It means flagging inefficiencies in your current portfolio even when fixing them might reduce billable hours. It means being invested in your program’s success in a way that extends well beyond the audit window. That kind of relationship is harder to find and worth a lot more than a lower invoice.
The bottom line
If you’re running multiple frameworks with multiple auditors and haven’t looked seriously at consolidation, here’s the honest summary: worst case, this is an 18-month journey to get everything coterminous. In practice, it’s largely pain-free — and on the other side of it, you’ve got hard dollar savings, happier engineers, a tighter audit window, and capacity to pursue additional certifications that actually move the business forward.
That’s not harmonization. That’s rationalization. And it’s worth doing.
Ready to rationalize your compliance program?
Talk to A-LIGN about how multi-framework consolidation can drive real ROI for your organization.
4 CMMC Myths Busted: What DIB Companies Need to Know in 2026
There is more disinformation circulating about CMMC right now than at any other point in the program’s history. Fear-based narratives about impossible deadlines, excessive costs, and assessor shortages are pushing some Defense Industrial Base (DIB) companies toward panic and others toward paralysis.
Over 1,000 organizations have now achieved CMMC Level 2 certification according to the CyberAB, the CMMC governing body, and thousands more have successfully self-assessed at Level 1 and Level 2 in the Supplier Performance Risk System (SPRS).
The companies succeeding are the ones grounded in facts, not noise. Here are four myths we are actively correcting from the assessor perspective:
Myth 1: November 2026 is a hard deadline, and you must be certified by then
This is the most pervasive and damaging misconception in the market right now — and it is accelerating.
November 10, 2026 is real, but what it represents is not what is being propagated. Phase 1 of the CMMC phased rollout began November 10, 2025. Phase 2, starting November 10, 2026, marks the next step in a deliberate phased rollout, where the Department of Defense (DoD) intends to include more Level 2 C3PAO certifications in applicable new DoD contracts and solicitations.
Here is the confirmed CMMC phase timeline per 32 CFR § 170.3(e):
- Phase 1: November 10, 2025: Level 1 and Level 2 self-assessments in applicable contracts. C3PAO assessments at DoD discretion.
- Phase 2: November 10, 2026: DoD intends to include Level 2 C3PAO certification requirements for applicable new contracts.
- Phase 3: November 10, 2027: Level 3 DIBCAC assessments introduced.
- Phase 4: November 10, 2028: Full implementation across all applicable DoD contracts.
Certification requirements are driven by what your specific contract solicitations require, not a universal calendar mandate.
What is real and what is already here: prime contractors are not waiting for any phase. Major primes are already requiring CMMC Level 2 third party certification as a supplier qualification condition right now, ahead of regulatory requirements. That is the actual forcing function for most of the DIB — not November 2026. The prime contractors are driving the timeline as a risk reduction and supplier eligibility measure.
Know what your contracts require and what your primes require. Those two answers define your real timeline, and for many organizations, that timeline is already here.
Myth 2: CMMC certification will cost you over $200,000
This number circulates as though it is a settled fact, but it is not — and the context behind it matters greatly.
According to DoD’s own cost projections cited across multiple industry sources, a Level 2 third-party certification, including the triennial C3PAO assessment and annual affirmations, is estimated in the range of $105,000 to $118,000 for most organizations, not $200,000. That figure carries a critical footnote that most vendors and articles omit entirely. The security controls CMMC validates are not a new cost of doing business with the DoD. They are the cost of being trusted with sensitive defense information in the first place.
DFARS clause 252.204-7012 required implementation of NIST SP 800-171 by December 31, 2017. If your organization handles Controlled Unclassified Information (CUI) under a DoD contract, those controls have been table stakes for nearly a decade. The DoD is not asking you to do something new. It is asking you to prove you are doing what you already agreed to do.
That is what CMMC is — validation. It’s not a new burden, but rather accountability for an existing one. The DoD is explicit on this point in the final rule. Implementation costs are excluded from CMMC cost estimates precisely because they should already have been incurred. Organizations conflating implementation costs with CMMC certification costs are either confused about the program or have a financial interest in that confusion.
Organizations that did the work — implemented the controls, maintained the System Security Plan (SSP), kept documentation current — are finding the certification cost manageable and consistent with DoD and industry estimates. Those treating CMMC as a starting point rather than a validation point are the ones experiencing shock and delay.
The investment is real. The $200,000 headline is not the baseline — it is what happens when preparation is treated as optional. Scope smart and come prepared. The cost follows the readiness.
Myth 3: Once you achieve CMMC certification, you are done
This may be the most dangerous myth of all, as it surfaces after the hard work is finished and exposes leadership and organizational liability.
CMMC Level 2 certification is valid for three years, but the certification is not the finish line — it is the baseline. The Affirming Official plays a critical and often underestimated role in maintaining that certification. Annual affirmations are required and binding. A senior official must formally attest that the organization continues to meet all CMMC security requirements regardless of required level. That affirmation carries legal weight. It is not a checkbox — it is accountability.
Cybersecurity posture naturally degrades. Personnel change, systems change, vendors change, and companies grow. An organization that was fully compliant on assessment day can drift significantly over 36 monthswithout active governance and continuous monitoring. There is also a False Claims Act dimension that every Affirming Official should understand. Knowingly affirming compliance when controls have lapsed is not a paperwork issue. Federal enforcement activity in this space is increasing. The affirmation is a legal attestation, and it should be treated accordingly.
The organizations that will recertify smoothly in three years are the ones treating CMMC as a continuous compliance program, not a one-time event. Build the governance now and maintain it. Annual affirmation should reflect reality, not hope or assumption.
Myth 4: There is a nationwide assessor backlog, and you cannot get scheduled
This narrative deserves a direct response from the assessor community.
A-LIGN is a large C3PAO with assessment bandwidth right now. As an authorized CMMC training partner, we can train and certify assessors internally to meet surge demand and we have been building toward that capacity for years. We are actively monitoring demand, and what we are seeing in the market is not an assessor backlog — it is a readiness gap.
Nearly every organization we engage with is not ready for assessment. Not because they haven’t tried, but because the foundational work that must precede a Level 2 C3PAO certification assessment is harder and more precise than most organizations realize. Common issues include incomplete SSPs, asset inventories that don’t match the network diagram, scoping that hasn’t been done in accordance with the DoD Scoping Guide, and evidence packages that aren’t “assessment ready.”
The pipeline of organizations that are prepared to undergo a Level 2 certification assessment is significantly smaller than the overall demand narrative suggests. Organizations that arrive prepared move efficiently through the process. Delays that get attributed to assessor capacity are more often the result of organizations that simply are not ready to be assessed.
Assessment bandwidth exists, but readiness is the limiting factor right now. The most valuable thing a DIB company can do right now is not chase an assessment slot, but to focus on getting ready for one.
The ground truth
More than 1,000 organizations have achieved CMMC Level 2 certification. The program is working. Assessment capacity exists, and affordable paths exist for organizations that come prepared and scope correctly. The DIB does not have a CMMC certification problem — it has a CMMC readiness and disinformation problem.
Readiness is the limiting factor. If your SSP is incomplete or your scope hasn’t been verified against the DoD’s Scoping Guide, now is the time to act. A-LIGN’s CMMC readiness assessment identifies gaps and ensures that when it’s time for a C3PAO assessment, it’s a validation of your work — not a discovery of new issues.
That is what getting certified in 2026 looks like. Reach out today to learn how A-LIGN’s CMMC readiness assessment can set you up for success.
Why Static OT Systems Need Proactive Penetration Testing
Operational technology (OT) systems are designed for longevity and redundancy. They power defense manufacturing and critical infrastructure, sometimes running unchanged for decades. But while your OT systems stay the same, the cyber threats aimed at them are always evolving and becoming more sophisticated. This creates a dangerous contradiction: the systems you trust for their stability are facing modern threats they were never built to withstand.
Many manufacturers stick to the “if it isn’t broken, don’t fix it” mentality, avoiding upgrades because they disrupt production or risk valuable equipment. But as your production environment remains static, attackers continually innovate, searching out new vulnerabilities and weak spots. In fact, manufacturing was one of the most targeted sectors, with CrowdStrike reporting a staggering 300% surge in cyberattacks in 2025.
This post explores the growing vulnerability of static OT environments. We will break down why traditional airgaps fail, how threats move laterally through your network, and why combining CMMC compliance with proactive penetration testing is the ultimate defense strategy for manufacturers.
The hidden risk in industrial security
The gap between long equipment lifecycles and fast-changing cyber threats is a major risk in industrial security. When you buy industrial machinery, you expect it to last for decades. But cyber threats change every few days or weeks.
Many industrial environments run legacy, unpatched, or entirely unsupported systems. You cannot easily upgrade these machines without halting production lines or causing operational disruptions. Sometimes, the update path hits a brick wall because modern operating systems lack driver support for your legacy equipment.
Consequently, defense manufacturers find themselves trapped. You must keep production moving to meet strict contract deadlines, but you are relying on systems that cannot defend against modern nation-state adversaries. Attackers from China, Russia, and Iran actively target these unpatched vulnerabilities to halt production or steal controlled unclassified information (CUI).
Why the airgap myth is failing
Historically, manufacturers relied on the “airgap” to protect their factory floors. The theory was simple: if the OT network does not connect to the internet, hackers cannot reach it.
Unfortunately, these physical separations erode over time. Remote access tools, vendor maintenance connections, and IT/OT integrations slowly bridge the gap between your corporate network and your factory floor. A technician might plug in a USB drive to run a diagnostic, or a vendor might request remote access to troubleshoot a malfunctioning sensor. Every new connection creates unseen exposure that attackers actively scan for and exploit.
Once an attacker breaches the IT network through a phishing email or compromised credential, the threat of lateral movement becomes very real. Flat networks allow adversaries to jump from a standard corporate laptop straight into the production systems. Because legacy OT systems lack modern security controls, the attacker faces almost no resistance once they cross that boundary and can often remain undetected.
Why CMMC compliance demands penetration testing
Defense manufacturers already invest serious time and money into compliance frameworks like the Cybersecurity Maturity Model Certification (CMMC). CMMC provides a vital foundation. It defines exactly where your sensitive data lives, how your systems connect, and which controls keep your environment safe.
However, compliance alone does not guarantee security. CMMC certification shows your controls are in place, but it doesn’t guarantee they’ll hold up against real-world attacks. This is where penetration testing becomes essential. Think of it as a stress test for your entire operation. A penetration test cuts through the theory and validates whether the controls you just spent months certifying can actually stop a real-world adversary in their tracks. It reveals how an attacker might chain together small misconfigurations to access your most critical manufacturing equipment.
Bridging the gap: CMMC and penetration testing
Too often, defense manufacturers treat compliance and security as totally separate projects. They use different vendors, different timelines, and different scoping exercises. This results in duplicated effort, fragmented reporting, and remediation advice that ignores your compliance framework.
When your CMMC assessor and your penetration tester understand your business context, everything becomes more efficient. CMMC already does the heavy lifting of defining your system boundaries and control implementations. When you build your penetration test on that exact same foundation, the findings transition from theoretical vulnerabilities to operational reality.
For organizations pursuing CMMC Level 2, penetration testing serves as the most rigorous way to validate your certified controls. It gives your Affirming Official real, objective evidence to stand behind during annual attestations. For those pursuing CMMC Level 3, annual penetration testing is an explicit mandate.
Building a cohesive defense strategy
When you bring penetration testing and CMMC compliance together, you get a holistic approach to securing your OT environment. CMMC sets the standard for how sensitive systems and data must be managed, while penetration testing proves that your controls actually work against real threats.
This powerful combination ensures you are not just checking boxes for certification — you’re identifying and fixing the gaps before adversaries can exploit them. For defense manufacturers, integrating these two practices means stronger, more reliable protection for core operations, compliance-ready evidence for assessors, and confidence that both cyber and regulatory risks are being addressed proactively.
Secure your OT environment
Your OT systems may need to stay static, but your security strategy must remain dynamic. Relying on eroded airgaps and outdated operating systems leaves your production floor exposed to devastating supply chain disruptions and contract penalties.
Do not wait for an adversary to test your defenses. By combining CMMC compliance with targeted, manufacturing-specific penetration testing, you can secure your environment and protect your most critical assets.
Take control of your industrial security posture. Reach out to the A-LIGN team today to schedule a penetration test that maps directly to your CMMC controls, and give your organization the confidence it needs to withstand modern cyber threats.
What the EU AI Act Enforcement Delay Actually Means for Your Organization
The European Commission, Council, and Parliament have all signaled support for pushing the EU AI Act’s high-risk enforcement deadline to December 2027. For many organizations, that news has prompted a pause on compliance planning, but that response could become costly.
For many organizations, this extension feels like a break. In reality, treating this delay as permission to pause your compliance planning is a strategic error. The shift is not an extension for businesses. It is a warning about the complexities of the regulatory landscape.
Here is what organizations need to understand about the delay, what the current timeline looks like, and what steps to take now to stay ahead of enforcement.
Why the deadline was extended — and why it matters
The extension was not a concession to industry but rather an acknowledgment that the regulatory infrastructure is not yet ready. National competent authorities remain partially designated, and accredited bodies capable of conducting conformity assessments are still in short supply. The ecosystem required for companies to demonstrate compliance simply does not yet exist at scale.
However, the core obligations under the EU AI Act remain unchanged. The regulatory direction is consistent — the only difference is the extended timeline. Organizations that view this extra runway as justification to slow their compliance efforts are assuming substantial operational risk, which may become unmanageable as enforcement nears and assessor availability tightens by late 2026.
The technical file required under Article 11 is not a checklist you can complete at the last minute. It is a robust body of documentation, demonstrating your system’s design decisions, training data governance, and fundamental rights impact assessments. Organizations that begin this process now will accumulate credible evidence over time, while those who wait until mid-2027 will find themselves scrambling to assemble it under significant pressure.
Current EU AI Act timeline
The current timeline includes several key milestones:
- August 2, 2026: Current legal deadline for Annex III (high-risk) systems
- December 2, 2027: Proposed deadline backstop for standalone high-risk systems
- August 2, 2028: Proposed extended deadline for product-embedded systems
It is critical to note that the Digital Omnibus proposal has not been formally adopted. The Digital Omnibus is a broad legislative package proposed by the European Commission that aims to align various digital rules and officially adjust timelines for directives like the EU AI Act. Because these negotiations and trilogues between the Parliament and Council have not concluded, August 2, 2026, remains the legally binding deadline for Annex III systems today.
Any executive who treats the 2027 date as settled law is operating on legislative optimism rather than legal fact. The prudent posture is to plan as though the extended deadlines will hold, while aggressively preparing as if they might not.
What organizations should do now
The period between now and enforcement is your implementation runway. Organizations that invest this time in building robust governance infrastructure will be best equipped for 2027 — while those who delay and scramble to create documentation at the last minute will fall behind.
Build and maintain an AI system inventory
Begin with a comprehensive AI system inventory. Any organization operating in or serving European markets must have a documented and organized list of all AI systems in use.
You should map this inventory to the Act’s risk tiers and clearly define whether your organization is acting as a provider, deployer, or both. When a market surveillance authority requests details about your AI systems and their compliance obligations, you must have a documented, readily available answer. Delaying this foundational work only increases risk — no extension will compensate for a lack of visibility into your own technology.
Implement an ISO 42001 AI Management System
Implementing an ISO 42001 AI Management System (AIMS) is one of the most impactful steps your compliance team can take right now. By establishing this system early, you build reliable, auditable evidence over time, setting your organization up for lasting compliance success.
An AIMS that has been operating for two years or more before enforcement creates a much stronger foundation for compliance than one assembled last-minute. Its governance framework, risk management routines, and documentation practices closely align with the EU AI Act’s requirements, and the resulting audit trail becomes more robust as your organization matures.
Address your Article 11 technical documentation gaps
Conduct a thorough gap analysis of your current technical documentation to ensure alignment with Article 11 requirements. Under the EU AI Act, Article 11 mandates that providers of high-risk AI systems must draft and maintain comprehensive technical documentation before placing their systems on the market. This requirement ensures you clearly document how your system works, its architectural design, and your data training and testing methods to prove it complies with the law.
This assessment is especially critical for high-risk systems. Gather comprehensive system design documentation, maintain records on training data governance, and ensure accuracy and robustness testing artifacts are in place. Conduct fundamental rights impact assessments as part of your process. These critical documents result from mature governance practices that must be established well before any regulatory deadline.
Identify your conformity assessment pathway
Identify which of your high-risk systems require third-party conformity assessment and which can proceed via self-assessment. Make this determination early in your compliance process.
Start building relationships with accredited assessment bodies as soon as possible. The pool of qualified assessors is limited, and demand will surge as enforcement draws near. Engaging an assessor early helps ensure you won’t be left waiting when capacity constraints arise.
Common mistakes to avoid
Organizations preparing for EU AI Act compliance often encounter common pitfalls — steps that seem productive on the surface but actually introduce hidden risks and gaps.
Treating ISO 42001 as a substitute for EU AI Act conformity
ISO 42001 certification shows your organization has a strong AIMS in place. While it does not replace full EU AI Act conformity, establishing this framework early can position your organization well as you build toward complete compliance.
Certification alone does not result in a compliant technical file, fulfill the conformity assessment requirements under Article 43, or substitute for the system-specific risk management documentation required by Article 9. These elements are interconnected but represent distinct layers of your compliance architecture. Treating them as interchangeable can lead to critical gaps that become apparent during regulatory scrutiny.
Scoping your AI Management System too narrowly
It can be tempting to define your AIMS scope too narrowly in hopes of minimizing audit demands, but this approach is a significant governance misstep.
A scope statement that leaves out your highest-risk systems carries real consequences. When you exclude critical systems from your AIMS scope, those systems lose the benefits of governance protections, documented evidence, and ongoing improvement that the standard provides. Scope your AIMS thoughtfully and comprehensively, then commit to building the operational maturity needed to support and sustain that scope.
The business case for acting now
Beyond mitigating regulatory fines, investing in AI governance infrastructure now presents a strong commercial advantage.
Enterprise customers in regulated industries are already weighing AI governance maturity in their vendor selection processes. Achieving ISO 42001 certification sends a clear, credible signal to the market —demonstrating your organization’s commitment to AI risk management long before enforcement deadlines loom. This certification can set you apart from competitors, helping to build trust with customers and partners and positioning your business as a leader in responsible AI.
For organizations already running ISO 27001 or ISO 27701 management systems, expanding to include AI governance offers significant efficiencies. You can leverage existing audit cycles, documentation infrastructure, and risk management frameworks — meaning the additional effort and cost to implement ISO 42001 is far lower than building a separate system. Integrating your approach not only saves resources but also creates stronger, more effective governance across the business.
Getting started
The enforcement deadline is a trailing sign of regulatory progress, not an indicator of how prepared your organization should be. The organizations best positioned in December 2027 will be those that start building their compliance programs now — not those who wait until the last minute to act.
A-LIGN supports organizations at every stage of AI governance maturity — from conducting initial system inventories and ISO 42001 readiness assessments to achieving full certification and preparing for EU AI Act compliance. If you’re ready to turn compliance obligations into a competitive edge, connect with our team today.
Guide to Audit Harmonization
Compliance teams today face a burgeoning portfolio of assessments and frameworks to manage, leaving them strapped for time and thinking strategically about their approach to compliance.
According to the 2026 Compliance Benchmark Report, one in four organizations cite managing multiple concurrent audits as their primary challenge. This challenge supersedes industry, with 97% of organizations conducting two or more audits per year, while 72% of enterprises conduct four or more audits each year.
Cultivating a high-quality compliance program isn’t a one-time process, it’s an ongoing operation. Audit harmonization can help teams drive efficiencies and meet the high expectations that executives, customers, and other stakeholders have of final reports and the audit experience. This approach identifies commonalities between frameworks to reduce duplicative work and save your organization time and money in the process.
Read on to learn:
- The benefits of audit harmonization
- A guide to audit harmonization
- Real-world examples of audit harmonization
Download our Guide to Audit Harmonization to follow along.
What is audit harmonization?
Audit harmonization is a white-glove approach to simplifying the audit process that is designed for organizations conducting three or more audits per year. This process includes one-on-one time with professionals who can identify overlaps and streamline even the most complex compliance strategies.
Benefits of audit harmonization
The 2026 Compliance Benchmark Report found that 99% of organizations believe that consolidating audits could save them time, and they would be right.
A-LIGN’S audit harmonization process synchronizes efforts across frameworks to:
Align business and compliance objectives
We create a compliance strategy with a custom solution to your compliance hurdles that drives efficiency and business outcomes. We lead interim strategic workshops for continual improvement and evolution of your compliance program.
Simplify transition and consolidation
Our customized transition process ensures a seamless migration. We identify overlapping requirements, requests, and subject‑matter interviews.
Provide a seamless, white‑glove audit experience
A dedicated team with a central point of contact provides tailored guidance and consistent resourcing to build a deep understanding of your business.
Who can execute audit harmonization?
Audit harmonization can be achieved with an experienced, trusted audit partner that can educate your organization about what the process looks like, identify areas for improvement, and streamline the audit process.
Defining a successful audit harmonization process
There are three key elements to a successful audit harmonization engagement:
- People: The people you enlist to complete your audit harmonization process should be experienced professionals that have a track record of success. Beyond this, however, these people should work well with your organization. The communication style and frequency should align with your goals.
- Process: A well-defined process out of the gate will lead to stronger outcomes from your audit harmonization process. This element is strongly tied to the audit partner you choose to work with, so be sure to enlist the help of an experienced firm
- Technology: Technology helps auditors work smarter to give you a high-quality final report in a quicker timeframe and with more assurance.
What do these look like in practice? There are five key steps to harmonizing audits through people, process and technology:
- Preparation
- Planning
- Fieldwork
- Report
- Post-audit touchpoint
Each of these processes are driven by people and technology to ensure you have a successful audit harmonization engagement.

How to get started with audit harmonization
Not sure how to get started? According to the Compliance Benchmark Report, 27% of organizations are in the same position. But choosing the right partner to educate and guide you through the process can ensure your organization is set up for success. Download our Guide to Audit Harmonization for more.
Taking the time to find the right partner to execute this process is essential. We recommend looking for the following qualities in a potential auditor:
- Breadth and depth of services: It’s important to pick a provider that can grow with you as your compliance strategy evolves. This will help your team achieve your goals sooner with less repeated effort.
- Tech-enabled: Although technology used to be the future of compliance, it’s now the standard. Choosing a partner that is enabled by an in-house audit management platform or integrated with a GRC/readiness tool.
- Clear audit process: The right audit partner should be able to give you a clear timeline and scoping, streamline the process, and align with the communication frequency and style of your team.
SAS improves audit harmonization and efficiency with A-LIGN
SAS is a global leader in data and AI, delivering and operating mission‑critical software solutions for major industries across the globe. SAS aims to drive its Governance, Risk and Compliance (GRC) program through automation, technology, and rigorous metrics, ensuring they can meet new certification and assurance demands without sacrificing speed or quality.
To streamline its compliance efforts and enhance operational efficiency, SAS actively participates in A-LIGN’s audit harmonization program. This initiative helps SAS consolidate over 10 certifications and attestations into a unified, cohesive process.
The challenge
To maintain trust and security across such a vast operation, SAS relies on its GRC-A team (Governance, Risk, Compliance, and Audit) to manage a complex landscape of public sector and commercial compliance requirements.
While the program’s primary mandates include risk reduction and strict adherence to internal controls, an overarching goal of the GRC-A program is to drive operational efficiency in their processes.
As SAS expanded its certification and assurance engagements, the GRC-A team looked to increase its auditing intake and capabilities.
SAS required a focused, long-term strategy that examined compliance obligations across a multi-year horizon.
“There’s no way that we could do all of our assurance engagements if we did them contiguously. There’s just not enough time in the year – A-LIGN harmonized our audit efforts, greatly saving our team valuable time and resources.”
-Cathy Smith, Senior Director of GRC-A
Why A-LIGN
SAS selected A-LIGN as its audit provider based on a shared long-term strategic vision and a commitment to growing together as assurance needs evolved. From the beginning of the relationship , A-LIGN demonstrated an understanding that SAS’ audit and compliance requirements would expand over time and positioned itself as a strategic partner rather than a transactional service provider.
Rather than focusing solely on immediate audit needs, A-LIGN engaged SAS in forward-looking discussions about business growth, evolving risk profiles, and anticipated assurance demands over the coming years. This approach established a foundation of trust and alignment, enabling the relationship to mature as the scope, complexity, and volume of assurance engagements increased.
As SAS’s assurance program grew, audit harmonization developed as a strategic response to managing multiple frameworks more effectively. A-LIGN’s ability to consolidate and align compliance efforts through its audit harmonization program allowed SAS to increase efficiency, reduce redundancy, and maintain consistency across engagements. By providing an integrated, tailored compliance framework for organizations managing three or more standards, A-LIGN supported SAS in developing a more scalable, sustainable, and mature compliance program aligned with long-term business objectives.
Additionally, SAS found A-LIGN’s A-SCEND audit management platform would play an essential part in streamlining and managing complex, multi-month engagements.
The results
A-LIGN’s audit harmonization methodology helped SAS streamline multiple audits including, but not limited to — SOC, ISO, FISMA, FedRAMP, and penetration testing engagements — by conducting them simultaneously. This approach maximized efficiency, transforming a traditionally year-long process into streamlined windows that reduced both time and cost, delivering significant gains for SAS’ GRC-A team.
Audit harmonization also improved collaboration between the GRC-A team and the internal IT organization. Instead of conducting multiple audits, the process was consolidated into single interviews or evidence pulls, minimizing disruptions and respecting the IT team’s time.
The A-SCEND platform further enhanced efficiency as it is designed to support organizations operating across multiple compliance frameworks by mapping evidence once and reusing it across audits (e.g., SOC 2, ISO 27001, FedRAMP). This significantly reduced duplicative requests and enabled a harmonized audit experience as assurance programs scale.
Additionally, A-SCEND’s AI capabilities helped SAS identify if existing evidence met new audit requirements or if prior evidence remained valid, reducing redundant work and increasing overall productivity.
As the global compliance landscape evolves, SAS is confident in its strategy, where meticulous planning, advanced technology, and strategic partnerships clear the path for sustainable growth.
Why A-LIGN
A-LIGN is the leading provider of high-quality, efficient cybersecurity compliance programs.
Our more than 400 global auditors have completed more than 36,00 audits and have more than 20 years of experience providing the best quality audit experience and final reports, exemplified through A-LIGN’s 96% customer satisfaction rating.
A-LIGN’s white glove audit harmonization process ensures that your organization can get back to work instead of completing duplicative work. Our industry-leading audit management software, A-SCEND, powers our best-in-class audit experience.
With A-LIGN, you can achieve your compliance goals with confidence and earn a report that your buyers can trust, with support from technology that streamlines the process. Ready to learn more? Contact us today.
FedRAMP 20x: What It Is, How It Differs from Rev. 5, and Where It Stands Today
Traditional FedRAMP pathways have long been criticized for being slow, manual, and documentation heavy. Even if you had the time, money, and effort to go through the authorization process, the larger question always loomed: “Can I find a Federal Agency “Sponsor” to partner with me through the Authority to Operate (ATO) process?”
Enter FedRAMP 20x — a new assessment and authorization path being developed in collaboration with industry and government. Its main goal? Rapidly increase the size of the FedRAMP Marketplace for agencies to be able to use the best Cloud Service Offerings (CSOs) commercially available, while maintaining protection over unclassified information.
In this post, we’ll explain what FedRAMP 20x is, how it differs from the existing Rev. 5 model, and where the program stands today — including the official phase structure and timelines.
What Is FedRAMP 20x?
FedRAMP 20x is an initiative by the GSA to build new FedRAMP authorization paths, streamline processes through automation, and encourage government-wide adoption of commercial cloud services. Instead of the traditional document-centric process, 20x leans into machine-readable evidence and automation, which has shown significantly shorter time to authorization in the pilot compared to legacy pathways.
Not only does it reimagine the documentation process, but it flips the entire security review process on its head. Instead of reviewing via the control-by-control narrative approach, it has developed “Key Security Indicators” (KSIs), which are a set of security capabilities that focus on measurable outcomes instead of prescriptive processes.
It’s important to note that the 20x program is currently being developed, as it’s going through its pilot phases with the goal of becoming publicly available Q3 of 2026.
How the legacy FedRAMP pathway operates
The traditional FedRAMP authorization model is rooted in National Institute of Standards and Technology SP 800-53 Rev. 5 controls and emphasizes thorough documentation, manual review, and compliance reporting.
Key characteristics of the Rev. 5 pathway include:
- Extensive System Security Plan (SSP) documentation
- Manual narrative evidence review
- Agency partner or “sponsorship”
- Iterative PMO review cycles
These aspects build high assurance but often at the expense of speed and cost.
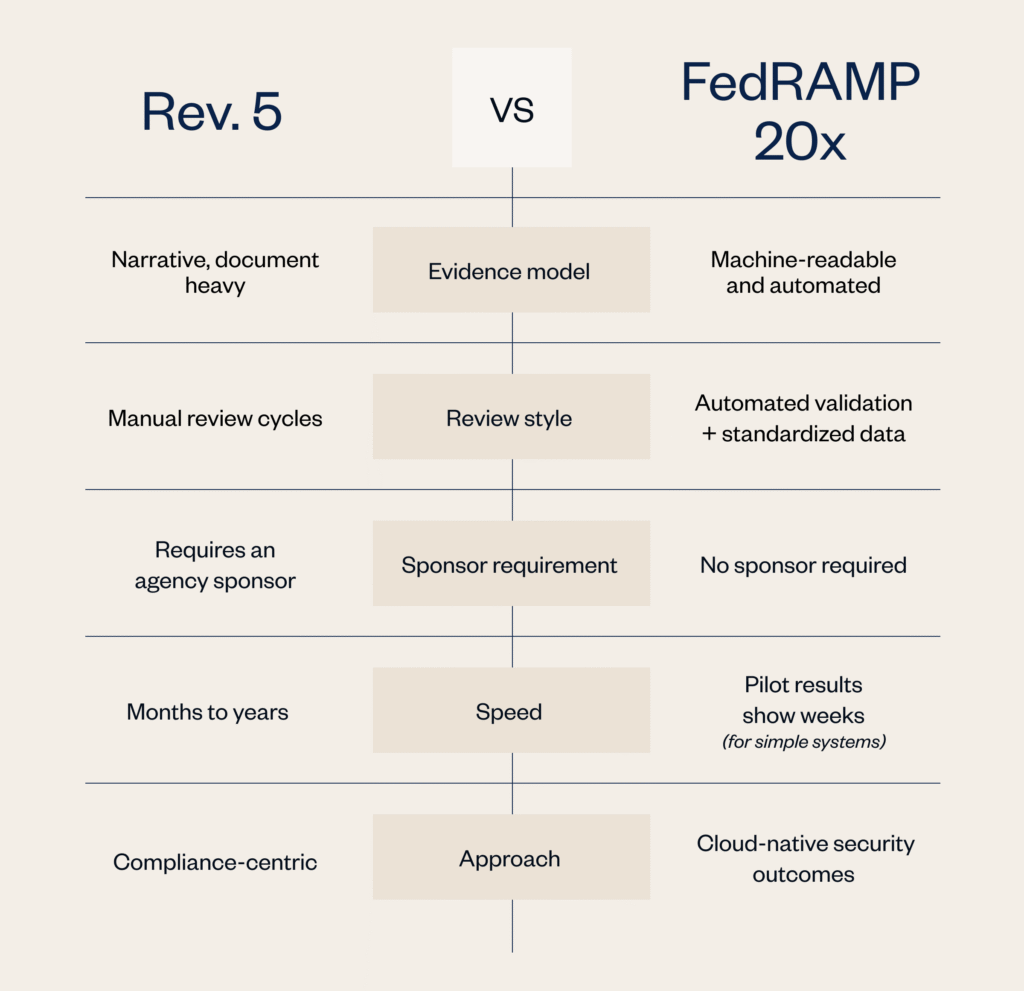
FedRAMP 20x vs Rev. 5: Key differences
FedRAMP 20x is not a “shortcut”— it’s a different pathway that prioritizes automation over narrative descriptions and manual reviewer interpretation. Here’s a quick look at how the legacy process works compared to 20x:
FedRAMP 20x phases and status
FedRAMP 20x is being delivered in phases, each with specific goals and pilots. Official documentation notes that timelines are estimated and subject to change based on real-world feedback.
Phase 1 – FedRAMP 20x Low pilot (completed)
Tested the first version of the 20x approach with Low impact authorizations, introducing machine-readable evidence and alternative validation methods.
A-LIGN participated as a 3PAO assessor of 20x Low systems as well as getting their own audit management software, A-SCEND, 20x Low Authorized.
Phase 2 – FedRAMP 20x Moderate pilot (active / current)
Participation was limited and not open to the general public; 13 selected CSPs from the Phase 1 20x Low pilot are working with FedRAMP and assessors to test the approach. That approach focuses on Moderate impact systems using automation and Key Security Indicators (KSIs).
The goals of Phase 2 are to:
- Test how CSPs can effectively meet automated validation requirements for initial and ongoing FedRAMP Authorization
- Test how these automated capabilities can be effectively assessed by third parties
- Understand how providers and assessors can work together to deliver innovative evidence of the ongoing security decisions within a cloud service
This is active and estimated to operate through Q2 of 2026.
What’s next (estimated goals)
While the published timeline from FedRAMP outlines estimated goals, they’ve also introduced a new naming convention for certification classes. The terms “Low,” “Moderate,” and “High” are being replaced with the following:
- Class A: Replaces FedRAMP Ready
- Class B: Replaces Low
- Class C: Replaces Moderate
- Class D: Replaces High
Additionally, there will now be a single certification name called FedRAMP Certified, as the “FedRAMP Validated” naming convention has been dropped.
Here’s what will come next after the current Phase 2 pilot ends:
Phase 3 – Wide-scale adoption of Class B and Class C
This is the phase in which Class B and Class C authorizations will become publicly available. Before that can happen, FedRAMP will formalize all Class B and Class C requirements based on the outcomes of Phase 1 and Phase 2.
This is estimated to happen in Q3-Q4 of 2026.
Phase 4 – Class D pilot
While the Class B and Class C authorizations continue, the pilot program for Class D authorizations will begin. This is targeted at hyperscale IaaS and PaaS providers, according to FedRAMP.
Note: During this phase, all Rev. 5 Authorized providers will be required to transition to machine-readable authorization data for both initial and continuing authorization.
This is estimated to happen in Q1-Q2 of 2027.
Phase 5 – End of life for new Rev. 5 authorizations
FedRAMP will stop accepting new Rev. 5-based agency authorization at the end of this phase. FedRAMP will also provide a clear path and timeline for ensuring all legacy Rev. 5 Authorized CSOs can transition to a 20x-based authorization. The deadlines for transitioning are not defined but are stated as “likely to include multi-year deadlines”
This phase is estimated to happen in Q3-Q4 of 2027.
Note: FedRAMP emphasizes that these timelines are goals and may shift as the program learns from pilot feedback.
What this means for cloud providers
Early planners: Understand that 20x is not fully baked, but the direction is clear and will be publicly available soon. Automation and machine-readable evidence are becoming central, even if you are planning for a Rev. 5 Authorization.
Mid-Rev. 5 authorizing CSPs: Don’t assume you can pivot lanes mid-process without analysis, but be sure to build awareness of 20x and how it may impact future offerings.
Already authorized providers: Monitor how reauthorization and continuous monitoring under 20x pilots evolve. Plan for a transition to machine-readable authorization data.
Across the board, treating 20x as “something to keep an eye on” is no longer sufficient — it should be part of your compliance roadmap for 2026 and beyond.
Strategic takeaway
FedRAMP 20x represents a generational shift in federal cloud authorization — one rooted in automation, standardization, and scalable evidence models. It’s still in pilot, but its goals are ambitious:
- Lower administrative friction
- Support faster adoption of secure cloud tech
- Enable more providers to participate in the federal market
Planning now will save tactical scramble later.




