What’s New with ISO 27002:2022?

On February 15, 2022, the International Organization for Standardization (ISO) released an update to ISO/IEC (International Electrotechnical Commission) 27002:2013 under the name ISO/IEC 27002:2022. The release of this new standard has caused a lot of confusion and anxiety within companies, with many under the mistaken impression that they’ll have to undergo a new certification process in order to achieve compliance. This, however, is not true.
In this blog, I’ll shed light on the new standard and explain what ISO 27002:2022 means for your business.
What Is ISO 27002?
Let’s start by clarifying that ISO 27002 should be viewed as more of a manual as it offers extensive guidance on the Annex A controls and best practices an organization should implement to ensure the confidentiality, integrity, and availability (CIA) of assets.
ISO 27001, on the other hand, actually establishes the compliance requirements needed to become certified. This clarification is important, primarily because ISO 27001 has not been updated yet, only its supplemental guidebook ISO 27002 has changed. This is, however, a great time for organizations to implement the best practices found in the revamped guidebook as we expect ISO 27001 will also be updated fairly soon.
Why Was ISO 27002 Updated?
Updates to ISO standards occur periodically. ISO/IEC 27002 has origins that trace back to a 1990’s UK government initiative. It was first a standard developed by the oil company Shell Energy that was donated to the UK and became a British standard in the mid-1990s ISO 27002 was adopted as an ISO standard in the year 2000 and seems to undergo revisions on an eight/nine-year cycle with official updates to ISO 27002 occurring in 2005, 2013, and now in 2022.
This most recent update reimagines the terminology and format of ISO 27002 to make it easier for the layperson to understand. There’s also more focus on cybersecurity and privacy, better aligning the controls to the modern digital era.
What Are the Major Changes?
While ISO 27002:2022 is an exhaustive guide with numerous changes, there are six changes in particular of which organizations should be aware.
1. Reduced Total Controls
There were previously 114 internal controls listed in ISO 27002:2013. Now, 57 of the controls have been consolidated, leaving just 24 controls to eliminate redundancies. It’s worth noting that while the number of controls has decreased, no controls were excluded, only merged for simplicity. And with the addition of some new controls, the total number now stands at 93.
2. 11 New Controls
The 93 total controls include 11 brand new controls that address:
- Information security for use of cloud services
- ICT readiness for business continuity
- Physical security monitoring
- Configuration management
- Information deletion
- Data masking
- Data leakage prevention
- Monitoring activities
- Web filtering
- Secure coding
- Threat Intelligence
3. Domains Have Become Categories
Say goodbye to confusing domains and hello to categories. Now, instead of 14 domains, each of the internal controls fall under one or more of the following four categories:
- Organization
- People
- Physical
- Technological
4. “Objectives” Have Become “Purpose”
Don’t expect to find the word “objective” as you would have in previous versions of the standard. Instead, you’ll find each of the controls have an intended “purpose.” This new framing was done intentionally to help organizations better understand the point of the control and its impact on your assets.
5. New Attributes Tables
ISO created a table of attributes that correspond with each control. The five categories of attributes are as followed:
Control type
What type of effect does the control have?
Preventive, Detective, or Corrective
Information security properties
Which part(s) of the CIA triangle does the control touch?
Confidentiality, Integrity, or Availability
Cybersecurity concepts
What type of cybersecurity action will be taken?
Identify, Protect, Detect, Respond, or Recover
Operational capabilities
Which of the following security specialization(s) does the control belong to?
Governance, Asset management, Information protection, Human resource security, Physical security, System and network security, Application security, Secure configuration, Identity and access management, Threat and vulnerability management, Continuity, Supplier relationships security, Legal and compliance, Information security event management, and Information security assurance
Security domains
Which information security field is involved?
Governance and ecosystem, Protection, Defense, or Resilience
6. Two New Annexes
Although there’s been a lot of consolidations, additions, and renaming of controls, ISO has made it easy to map the controls back to the 2013 version. With Annex B, users can find a 2022 control and then see with which 2013 control it corresponds. The reverse is true with Annex A, which allows users to first select a 2013 control and find the 2022 control with which it corresponds.
Get Ready for Certification
Although no action needs to be taken today, the updates to ISO 27002:2022 present a great opportunity for organizations to start reviewing and updating their internal controls. Doing so now, ahead of the anticipated ISO 27001 update, will enable organizations to more efficiently implement best practices to achieve compliance in the future. Certification bodies will require a shift once ISO 27001 has been updated but as always, being prepared is key to cybersecurity compliance success!
To expand your knowledge on how to achieve compliance, check out what it takes to get certified in 5 Steps to ISO Certification.
Understanding Federal Supply Chain Risk Management
Federal supply chain risk management remains a critical focus as cyber-enabled supply chain attacks continue to evolve in sophistication and frequency. These threats, often used as tools of hybrid warfare, pose significant risks to national security. While the principles of supply chain risk management (SCRM), cyber SCRM (C-SCRM), and federal SCRM share common ground, federal SCRM carries heightened stakes due to its direct implications for the security and resilience of the United States.
To grasp the ongoing efforts to strengthen federal supply chain risk management, it’s essential to first understand how supply chain risk management is defined within the broader context of cybersecurity.
What is cyber supply chain risk management?
Cyber supply chain risk management (C-SCRM) is the continuous process of identifying, evaluating, and mitigating risks associated with an organization’s IT and software supply chains. It’s a critical, organization-wide effort that extends beyond the IT department, embedding security into the entire risk management framework to protect essential systems and data.
C-SCRM best practices
The National Institute of Standards and Technology (NIST) provides foundational guidance for C-SCRM. To build a resilient program, organizations should prioritize integrating C-SCRM across all business functions, establishing a formal and dynamic program, and deeply understanding their critical suppliers. Collaboration, continuous monitoring, and comprehensive resilience planning are also essential components of a strong C-SCRM posture.
Maintaining trustful and transparent relationships with suppliers is crucial, as your security is only as strong as its weakest link. Breaches originating from third parties, and even “fourth parties” (your vendors’ vendors), can dramatically increase the cost and impact of a security incident.
Strategies for effective C-SCRM
To navigate today’s complex threat landscape, organizations must adopt more advanced and proactive strategies.
- Adopt a zero-trust mentality: Operate under the assumption that a breach is inevitable. A zero-trust architecture requires strict verification for every user and device trying to access resources on your network, regardless of whether they are inside or outside the network perimeter.
- Leverage AI and automation: Use artificial intelligence and automation to enhance continuous monitoring. These technologies can analyze vast amounts of data to detect anomalies, predict potential threats, and automate responses, allowing for faster and more effective risk mitigation.
- Enhance vendor risk management: Go beyond initial security questionnaires. Clearly define security requirements in all contracts and RFPs, and demand evidence of compliance, such as penetration test reports or security certifications. Implement continuous monitoring to ensure vendors maintain their security controls over time.
- Create a comprehensive asset inventory: You cannot protect what you do not know you have. Maintain a thorough inventory of all assets — including hardware, software, data, and personnel — and map out where they interact with third parties to identify potential points of failure.
What is federal supply chain risk management?
Federal SCRM is the process of mitigating risks within the supply chain that could impact national security. While historically focused on the Department of Defense (DoD) and the Defense Industrial Base (DIB), the scope of federal SCRM has expanded.
This expansion is a direct response to the increasing sophistication of our nation’s adversaries. These actors exploit supply chain vulnerabilities to infiltrate systems, steal intellectual property, corrupt software, and surveil critical infrastructure, posing a direct threat to U.S. security.
Key frameworks: NIST 800-171 and CMMC
To counter these threats, the U.S. government has established specific cybersecurity standards. The National Institute of Standards and Technology (NIST) 800-171 provides a set of security controls for protecting Controlled Unclassified Information (CUI) in nonfederal systems. Federal contractors and subcontractors handling CUI must implement these controls to safeguard sensitive data.
Building on this foundation, the Cybersecurity Maturity Model Certification (CMMC) program was created to verify that contractors have the necessary protections in place. The self-attestation approach under the old DFARS Interim Rule proved insufficient, leading to the development of CMMC as a more robust verification method.
CMMC 2.0: The future of federal supply chain risk management
The Cybersecurity Maturity Model Certification (CMMC) is a framework designed to safeguard Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) within the Defense Industrial Base (DIB). With the release of CMMC 2.0 in October 2024, the framework has been streamlined into three levels of compliance, each tailored to the sensitivity of the information being handled:
- Level 1 (Foundational): Focuses on basic cybersecurity practices for organizations handling FCI. Compliance is demonstrated through annual self-assessments.
- Level 2 (Advanced): Designed for organizations managing CUI, this level aligns with the 110 practices outlined in NIST SP 800-171. Critical CUI handlers require third-party assessments every three years.
- Level 3 (Expert): Reserved for the most sensitive programs, this level incorporates additional requirements from NIST SP 800-172 and mandates direct assessments by the Department of Defense (DoD).
The publication of the 48 CFR rule has solidified the implementation of CMMC 2.0, outlining a phased rollout for mandatory compliance in new DoD contracts. However, it is crucial to note that contracting officers have the discretion to include CMMC requirements in their contracts ahead of this schedule. Some organizations are already seeing these requirements appear in Requests for Proposals (RFPs).
The official phased rollout is structured as follows:
- Phase 1 (Starts November 10, 2025): For the first 12 months after the rule’s effective date, Level 1 and Level 2 self-assessment requirements may be included in applicable solicitations and contracts as a condition of award.
- Phase 2 (Starts November 10, 2026): Over the next 12 months, Level 2 third-party assessment requirements (C3PAO Certification) will be widely introduced in solicitations and contracts as a condition of award.
- Phase 3 (Starts November 10, 2027): In this phase, Level 2 C3PAO Certification becomes a requirement for all applicable solicitations and contracts, including the exercising of option periods. Level 3 government-led (DIBCAC) assessment requirements will also be introduced.
- Phase 4 (Starts November 10, 2028): This marks the full implementation of all CMMC requirements (Level 1, 2, or 3) across all applicable DoD solicitations and contracts, including option periods.
This shift underscores the DoD’s commitment to mitigating supply chain risks and enhancing the resilience of federal supply chains. Organizations within the DIB must now be prepared to demonstrate their cybersecurity posture through either independent validation or self-assessment, depending on their assigned CMMC level.
How to prepare for CMMC certification
- Determine your organization’s CMMC level. Level 1 is for contractors and subcontractors processing FCI. Level 2 is for organizations processing CUI. Only organizations working on the DoD’s most sensitive programs will be expected to achieve Level 3 certification.
- Review the assessment guide for your CMMC level. The CMMC Level 1 Self-Assessment Guide and Level 2 Assessment Guide explain how contractors will be evaluated. Unfortunately, there is not yet an assessment guide for CMMC Level 3.
- Work with a tech-enabled organization to secure your data. Cybersecurity solutions like Summit7, Radicl, and CyberSheath can help you secure your FCI and CUI to prepare for CMMC compliance.
- Select a C3PAO and complete a readiness assessment. With a limited number of C3PAOs, it is important to start validating your organization’s readiness as soon as possible, as you will need time to remediate any gaps found.
- Engage a C3PAO for Level 2 Certification early. If your organization requires a CMMC Level 2 certification, engaging a C3PAO is a critical step. These assessors are already in high demand, and their schedules are filling up quickly. Waiting until the CMMC requirement appears in contracts will likely be too late, as you may face significant delays in finding an available C3PAO to conduct your assessment.
Work with a top federal assessor
Federal SCRM is no longer a future concern—it’s a present-day necessity. As the volume and sophistication of global cyberattacks rise, organizations are under increasing pressure to enhance their defenses and gain clear visibility into their supply chains. Third-party risk remains a significant threat, as many businesses unknowingly collaborate with vendors who have inadequate cybersecurity measures, creating vulnerabilities that can be exploited.
Navigating the complexities of federal compliance requires expertise. Whether you need guidance through the NIST 800-171 assessment process or assistance preparing for your CMMC certification, A-LIGN can help you take the most efficient path to compliance. As an authorized C3PAO with over 1,000 successful federal assessments completed, our team has the experience to help you strengthen your security posture and meet government requirements.
What Is Death Master File Certification?
Since late 2016, organizations have faced a stricter certification process to be granted access to the Death Master File (DMF), a computer database created by the United States’ Social Security Administration from 1962 to present day. The DMF is a protected file that includes information regarding the deceased such as their name, date of birth, date of death, social security number, last known zip code, if their death certification was observed, and other personal identifiable information (PII). For organizations who need to access to the PII of deceased individuals, they will need to certify with the DMF. Generally, in the three-year period following an individual’s death, sensitive information is unable to be released.
There are many challenges organizations can face when seeking DMF certification. Let’s review the certification process, what your organization should prepare for, and the standards against which you can certify.
What is the DMF certification process?
To access the DMF, an individual or entity must have a legitimate fraud prevention interest or have a legitimate business purpose to a law, government rule, regulation, or fiduciary duty. If an organization qualifies for DMF certification, they will be required to follow the steps below during their assessment process.
Step 1: Testing is conducted against SOC 2 or NIST 800 series standards.
Step 2: Organizations must go to the National Technical Information Service (NTIS) website to pay the required fees and will receive a processing number. Please note, these fees are in addition to those paid to the Accredited Conformity Assessment Body (ACAB) for attestation.
Step 3: Organizations must obtain the FM100A attestation form from the NTIS website and provide your auditing firm with the processing number to complete the attestation.
Step 4: Your auditor files the attestation documentation with NTIS. Your auditor will notify you that your form has been submitted and reaches out only if an issue arises. If all information is correct, NTIS communicates directly with your organization on approval/certification status.
What should my organization prepare for?
Once you achieve DMF certification, it doesn’t stop there. Your organization will need to be prepared for recertifications, unscheduled audits and more. Below is a list of what you can expect in the next several years following your initial DMF certification.
- Annual recertification by the organization seeking access
- Third-party conformity attestation every three years
- Agreement to scheduled and unscheduled audits, conducted by National Technical Information Service (NTIS) or the ACAB at the request of NTIS
- Fines up to $250,000 per year for noncompliance
The entity wishing to access the DMF must submit written attestation from an ACAB to prove that the appropriate systems, facilities and procedures are in place to safeguard information and maintain the confidentiality, security, and appropriate use of the information.
Subscriber certification must be completed annually. The LADMF Systems Safeguards Attestation Form must be completed every three years.
The U.S. Department of Commerce’s National Technical Information Service (NTIS), the governing body behind the DMF, can conduct both scheduled and unscheduled compliance audits and fine organizations up to $250,000 for noncompliance, with even higher penalties for willful violations. Due to the potential for substantial fines, it is important that entities be able to implement the appropriate systems’ facilities and procedures to safeguard the information.
What standards can organizations certify against?
Organizations can achieve certification by testing against standards such as SOC 2, and NIST 800 series publications.
What is SOC 2?
SOC 2 is a reporting standard that provides clients assurance regarding a service organization’s controls that do not affect the clients’ internal controls over financial reporting. This report is intended for use by stakeholders (customers, regulators, business partners, suppliers, directors) of the service organization to have a thorough understanding of the service organization and its internal controls.
What is NIST 800-53?
Published by the National Institute of Standards and Technology (NIST), NIST 800-53 covers the steps in the Risk Management Framework (RMF) that address security control selection for federal information systems in accordance with the security requirements in the Federal Information Processing Standard (FIPS) 200.
Helping You Achieve DMF Certification
A-LIGN is an ACAB that can attest to organizations’ systems and procedures in place. A-LIGN utilizes various published information security standards, mainly the AICPA SOC 2, to satisfy the rule’s audit requirements.
Since 2015, A-LIGN has been working to help our clients meet their DMF audit requirements and has successfully submitted the appropriate attestation forms to NTIS, resulting in certification for our clients. We have extensive experience testing the controls required by LADMF and can guide your organization through the certification process with ease.
FedRAMP FAQ – Understanding FedRAMP 2022
Any organization seeking to provide cloud products or solutions to a federal agency will need to go through a FedRAMP Readiness Assessment and then a full FedRAMP assessment to receive an Authorization to Operate (ATO) which ensures the security of its hosted information meets FedRAMP requirements. The Federal Risk and Authorization Management Program (FedRAMP) is a government-developed standardized approach to security assessment, authorization, and continuous monitoring of Cloud Service Providers (CSPs). Only Third Party Assessment Organizations (3PAO) may perform FedRAMP assessments.
Rather than needing multiple assessments, FedRAMP is an integrative standardized audit designed to be a common one-stop-shop for CSPs. FedRAMP follows the “do once, use many” methodology. FedRAMP’s myriad of benefits includes efficiency of resources, both cost effective and time-saving.
The goal of FedRAMP is to increase confidence in the security of cloud solutions through continuous monitoring and consistent use of best information security practices and procedures.
As organizations explore their federal audit options, A-LIGN’s experienced assessors have compiled and answered five frequently asked questions to help organizations better understand the assessment process.
1. Does FedRAMP apply to me?
Any Cloud Service Provider (CSP) that is currently or looking to become a third-party vendor for federal agencies must become FedRAMP certified. State government agencies may also require third-party CSPs to become FedRAMP certified. There is also the StateRAMP program for CSPs working with State governments.
2. Do CSPs need an agency sponsor to become FedRAMP certified?
Yes, there are two processes in which CSPs can become FedRAMP certified. The first is through an agency sponsorship when a government entity vouches for a CSP streamlining their approval process. The other option is for CSPs to go through the Joint Authorization Board (JAB) that includes a readiness assessment which reviews controls and upon passing provides joint provisional security authorization.
3. What are the key processes of FedRAMP?
The key processes of FedRAMP include a security assessment, leveraging and authorization, and ongoing assessment and authorization. The security assessment involves a set of requirements from the NIST 800-53 Rev. 4* controls to test security authorizations. In the FedRAMP repository, federal agencies view security authorization packages and leverage these packages to grant authorization. Once granted, continuous assessment and authorization, or continuous monitoring, activities must be in place to uphold authorization.
*FedRAMP will be transitioning to NIST SP 800-53 Rev. 5.
4. Is penetration testing mandatory for a FedRAMP ATO?
Yes, a penetration test is a mandatory part of the assessment process if the CSP is moderate or high-risk level impact. Third-Party Assessment Organization (3PAO) must perform mandated penetration testing.
5. How do I start the process of becoming FedRAMP certified?
The process is dependent on an organization’s current level of compliance with NIST SP 800-53 Rev. 4. If an organization has never written a System Security Plan (SSP), evaluating current security controls against the controls in the NIST SP 800-53 Rev. 4 is recommended.
Becoming FedRAMP Compliant
If you are a Cloud Service Provider (CSP) currently providing, or seeking to provide, services to federal agencies, A-LIGN can make your FedRAMP process seamless. We will support you during your entire FedRAMP journey, from readiness to authorization.
Does My European Business Need a FedRAMP Assessment?

You may have noticed the United States’ Federal Risk and Authorization Management Program (FedRAMP) is now gaining traction in other parts of the world. It begs the question, “Does my business need a FedRAMP assessment?”
FedRAMP was originally launched in 2011 as a way for the U.S. government to manage security risks as they adopt products and services that store, process, and transmit federal information in the cloud. Although FedRAMP is usually leveraged as a way for cloud service providers (CSPs) to meet Federal Information Security Modernization Act (FISMA) requirements, a growing number of organizations are using this risk-based standard to not only enhance their security, but to also stand out from the competition and win new business.
Let’s take a look at why a European business would want to pursue FedRAMP authorization and the many benefits to their organisation.
Why would a European business pursue FedRAMP Authorization?
There’s one main factor that most often motivates European businesses to pursue FedRAMP Authorization to Operate (ATO) status: They would like to sell a cloud service offering (CSO) to the U.S. government.
FedRAMP was specifically designed to ensure that CSPs with a software as a service (SaaS), platform as a service (PaaS), or infrastructure as a service (IaaS) CSO have adequate information security to do business with a U.S. federal agency. The specific requirements that a CSO must fulfil are dictated by FISMA and its subsequent memorandums.
In other words: If your business is a CSP that would like to sell a cloud-based solution to the U.S. government, you must obtain FedRAMP. Bonus- FedRAMP’s “do once, use many approach” means that when you achieve FedRAMP ATO status, your security package can be reused by any federal agency. You will also be listed in the FedRAMP Marketplace, which is often the first place federal agencies look when sourcing a new CSO.
What are the benefits of FedRAMP for European businesses?
Before we dive into the benefits, it’s worth noting that FedRAMP is not a quick and easy process that your business can sail through without much effort. It is a serious undertaking that requires patience as you work to fill your existing security gaps.
That being said, achieving FedRAMP ATO status comes with several advantages that make the effort required more than worth it. Here are a few to consider:
- The ability to re-use FedRAMP across multiple U.S. government agencies
- More robust security and risk mitigation for your CSO
- Enhanced real-time security visibility
- Improved trust among customers, prospects, and partners
- A marketing proof point that can be used in the private sector
Additionally, the new FedRAMP control baselines using NIST 800-53 Rev 5v uses an evolving, threat-based approach that allows CSPs to keep their information security efforts up to date against new and emerging threats.
How can my business get started with FedRAMP?
There are two options to choose from when looking to authorize a CSO through FedRAMP: a Joint Authorization Board (JAB) provisional authorization (P-ATO) or an ATO issued by an individual U.S. government agency. For more guidance on selecting your authorization strategy, I highly recommend reading through the FedRAMP CSP Authorization Playbook.
Below are the four high-level steps involved in the FedRAMP authorization process:
1. Document
Your business must categorize the CSO being considered for FedRAMP in accordance with NIST FIPS-199. The category (Low, Moderate, or High impact) that applies to your CSO depends on how much harm would be caused by a security breach. See our guide Understanding Federal Compliance for more details about these impact levels.
2. Assess
A federally-accredited third-party assessment organization (3PAO) conducts a security assessment to determine if your CSO meets the baseline controls required for FedRAMP. If they do meet the baseline controls, the 3PAO will submit an assessment package attesting to your compliance.
3. Authorize
The government agency will review the security package and either approve to organization as FedRAMP authorized or request additional testing. A final review is then conducted by the government agency and FedRAMP Program Management Office (PMO) to decide if they will accept the risk associated with the use of the CSO. If approved and accepted, Authorizing Officials will issue an ATO letter.
*For the P-ATO route, this review process will also include the FedRAMP JAB.
4. Continuously monitor
After authorization is granted, you must provide monthly deliverables to the agency (or agencies) using your CSO to demonstrate that your cloud security controls are continuing to operate effectively. You must also have a 3PAO complete an annual security assessment to ensure the system’s risk posture remains acceptable.
Work with a top FedRAMP assessor
While FedRAMP was created to assist the U.S. government to rapidly, rigorously, and consistently assess the security of cloud solutions, it also benefits CSPs. From earning more U.S. federal work to increasing trust among customers and prospects in the private sector, there are several reasons why your European business may want to pursue FedRAMP authorization.
Looking to firm up your plan for FedRAMP? As an accredited 3PAO that is one of the top five FedRAMP assessors in the world, A-LIGN is ready to perform your security assessment. In fact, we are currently a FedRAMP 3PAO for a growing number of European CSPs. If you have already chosen a 3PAO, but could use some guidance throughout the preparation process, our independent team of advisors can help you with control implementation, process documentation, and everything in between. Learn more about our comprehensive FedRAMP services.
SOC 2: Type 1 or Type 2?
As more customers ask for demonstrated SOC 2 compliance, independent cybersecurity control validation and attestation are becoming necessary to compete for high-priority contracts. Beyond customer demand, SOC 2 reports ensure that controls are properly implemented and used within your organization, greatly reducing potential security threats.
For organizations seeking a SOC 2 report, there are two attestation options available: Type 1 and Type 2. What type is best for your organization to prove compliance? Our experienced assessors break down the options so the path to SOC 2 compliance is clear.
What is a SOC 2 report?
A SOC 2 report highlights the controls in place that protect and secure an organization’s system or services used by its customers. The scope of a SOC 2 examination extends beyond the systems that have a financial impact, reaching all systems and tools used in support of the organization’s system or services. The security of your environment is based on the requirements within a SOC 2 examination, known as the Trust Services Criteria (TSC):
- Common Criteria/Security (required)
- Availability (optional)
- Processing Integrity (optional)
- Confidentiality (optional)
- Privacy (optional)
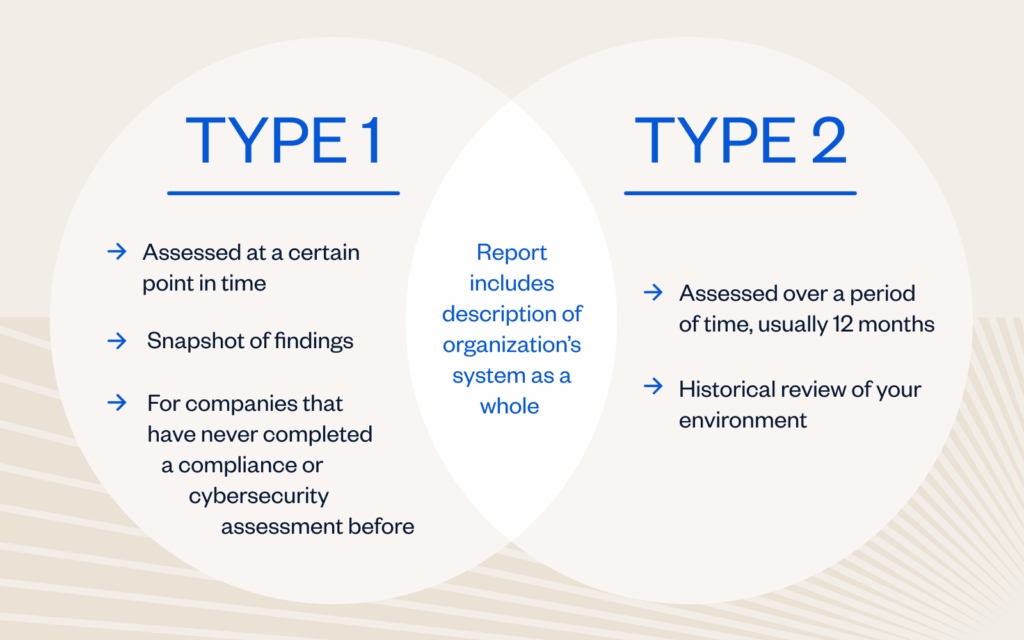
The difference between Type 1 and Type 2 reports
Which SOC 2 report should your organization choose? Read on to learn the difference.
SOC 2 Type 1 Report
Organizations that select a SOC 2 Type 1 report will evaluate the design and implementation of an organization’s system of internal controls as they relate to the in-scope TSCs. The report will include the management’s assertion, auditor’s opinion on the design and implementation of controls, a description of the in-scope system, and the controls that were independently tested by the auditor. This serves as a snapshot of an organization’s environment to determine if controls are suitably designed and in place.
SOC 2 Type 2 Report
SOC 2 Type 2 reports will evaluate the design, implementation and operating effectiveness of an organization’s system of internal control as they relate to the in-scope TSCs over a defined period of time, typically six to twelve months. The report will include the management’s assertion, auditor’s opinion on the design and operating effectiveness of controls, a description of the in-scope system, and the controls and test results that were independently tested by the auditor A SOC 2 Type 2 report provides a historical view of an organization’s environment to determine if the organization’s internal controls are designed and operating effectively.
What is a readiness assessment?
Now that you understand the difference between a Type 1 and Type 2 report, how can you best prepare for your SOC 2 examination? Consider these options from A-LIGN’s expert auditors:
- Traditional approach: A-LIGN will perform a formal Readiness Assessment that simulates a Type 1 or Type 2 audit and results in a report with recommendations from the auditor. This option is recommended for companies that don’t have many formal procedures or have never been through an audit before.
- Belay approach: This hybrid two-step approach has a smaller high-level gap assessment of key controls prior to the Type 1 SOC 2 examination. This approach saves time and costs and is designed for more mature organizations with formally established and implemented procedures who still have concerns or questions about their readiness for a SOC 2 audit.
Why A-LIGN?
A-LIGN is the leading provider of high-quality, efficient cybersecurity compliance programs. Combining experienced auditors and audit management technology, A-LIGN provides the widest breadth and depth of services including SOC 2, ISO 27001, HITRUST, FedRAMP, and PCI. A-LIGN is the number one issuer of SOC 2 and a leading HITRUST and FedRAMP assessor. The A-LIGN difference is:
- 17.5k+ SOC assessments completed
- #1 SOC 2 issuer in the world
- 200+ SOC auditors globally
Next steps
Ready to begin your compliance journey? Contact A-LIGN today to get started.
Updated FedRAMP Readiness Assessment Report Guide for 3PAOs – a Summary
Is a Cloud Service Provider (CSP) ready to undergo the extensive FedRAMP authorization process? That’s what the FedRAMP Readiness Assessment Report (RAR) intends to find out.
A Third Party Assessment Organization (3PAO) will leverage the RAR to document and validate a CSP’s full implementation of the technical capabilities required to meet FedRAMP security requirements. Let’s take a look at what’s involved in a FedRAMP Readiness Assessment and the steps outlined in the updated FedRAMP RAR guide.
What Does a FedRAMP Readiness Assessment Entail?
Completing a RAR requires a 3PAO, such as A-LIGN, to:
- Confirm full implementation of the Cloud Service Offering’s (CSO) technical capabilities
- Understand how a CSO works and operates
- Validate what is implemented within the CSO
- Understand the key functionalities of the CSO and document the RAR in a way that is comprehensible by agency customers that may not have a strong technical background
- Verify that the stated authorization boundary of the CSO and the data flows within the system are practical, secure, and logical
While a Readiness Assessment is intended to determine a CSO’s readiness to achieve FedRAMP authorization, it does not guarantee it. CSPs can use the process as an opportunity to discover and remediate any deficiencies in a CSO’s capabilities, as well.
The RAR must specifically, clearly, and succinctly provide an overview of the system as well as a subjective summary of a CSO’s overall readiness. This includes rationale such as notable strengths and other areas for consideration. The 3PAO should answer RAR requirements and questions, stating what they found (observations and evidence) during their review, and, most importantly, how they determined whether a CSP adequately addresses the question area.
In a thorough 19-page document, FedRAMP provided updated guidance as well as templates for 3PAOs evaluating CSPs for readiness. Below, you’ll find a summary of the 12 steps 3PAOs should follow when preparing a RAR as outlined in the new guidance.
1. Validate the Authorization Boundary
Assessing any CSO for readiness begins by determining whether the offering has a clearly defined and maintainable authorization boundary. It falls on 3PAOs to perform full authorization boundary validation to ensure nothing is missing from the CSP identified boundary, and all included items are present and part of the system boundary.
This step also extends to the need for 3PAOs to conduct a discovery scan. This is intended to identify operating systems running on the network then map them to IP addresses, identify open ports and services, and gather rudimentary information on targeted hosts.
2. Identify All Data Flows and Stores Within and Throughout the Authorization Boundary
A 3PAO must validate the data flow diagrams (DFDs) and provide a written description of the data flows. Each DFD must be high resolution, reflect the same components as the authorization boundary diagram, and explicitly identify every location where federal data and metadata is in relation to the 3PAO system authorization boundary.
3. Determine Leveraged FedRAMP Authorizations
For a FedRAMP-leveraged CSO, a 3PAO must provide the specific details regarding this relationship. The leveraged offering must be listed on the FedRAMP Marketplace with a status of Authorized (not FedRAMP Ready or In Process). An Authorized status can only be achieved upon approval of a full assessment package by the Joint Authorization Board (JAB) or the Project Management Office (PMO). If a 3PAO is assessing a SaaS then it must ensure that subscriptions to underlying services (IaaS, PaaS) are accurately documented.
4. Determine External and Corporate Systems and Services
Within the RAR, a 3PAO must indicate a CSP’s connections to external systems and services, including corporate systems and services that are not part of the authorization boundary. It must divulge the use of third-party providers and external services / systems lacking FedRAMP authorization at the time of RAR completion. The 3PAO will also need to provide a mini analysis of the RAR external leveraged services and its risks.
5. Application Programming Interfaces (APIs)
While they are connections, APIs have their own category within the RAR. 3PAOs must identify each API a CSO uses.
6. Assess and Describe the Strength of the Physical and/or Logical Separation Measures within the System
A 3PAO must make an assessment of physical and/or logical separation measures based on very strong evidence, such as the review of any existing penetration testing results, or an expert review of the products, architecture, and configurations. In the absence of a penetration test, a 3PAO must provide a rationale for being able to prove that there is adequate segregation of tenants and data. 3PAOs must also analyze all border devices to ensure they provide appropriate segregation from other systems, and describe the methods used to verify the strength of separation.
7. Ensure Federal Mandates Are Met
3PAOs assessing Moderate and High baseline systems must ensure six federal mandates are met.
- Are FIPS 140-2 Validated cryptographic modules (IAW SC-13) consistently used everywhere cryptography is required? This includes all SC-8, SC-8(1), and SC-28 required encryption.
- Does the system fully support user authentication via Agency Common Access Card (CAC) or Personal Identity Verification (PIV) credentials?
- Is the system operating at Digital Identity Level 3?
- Can the CSP consistently remediate High vulnerabilities within 30 days, Moderate vulnerabilities within 90 days, and Low vulnerabilities within 180 days?
- Does the CSP and system meet Federal Records Management Requirements, including the ability to support record holds, National Archives and Records Administration (NARA) requirements, and Freedom of Information Act (FOIA) requirements?
- Does the system’s external DNS solution support DNS Security Extensions (DNSSEC) to provide origin authentication and integrity verification assurances?
The answer must be “yes” for all six questions before submitting the RAR.
8. Ensure DNSSEC Is in Place
It is incumbent upon the 3PAO to verify that the external authoritative DNS server replies with valid Domain Name System Security Extensions (DNSSEC) responses. Additionally, any external domain used to access a CSO must be verified as registered with a DNSSEC signature. The authoritative server is signed by the Top-Level Domain server, which is in turn signed by the root server. The entire signature chain will be checked by the recursive server, so any broken signature breaks the whole chain.
9. Verify FIPS 140-2 Validated Encryption within and throughout the System Boundary
For FIPS 140-2 validated encryption, all Moderate and High-level federal data and metadata must be encrypted for all DAR and DIT within and throughout the system boundary. CSPs or vendors using FIPS 140-2 validated modules are required to have a certified security policy stating how their products must be used to ensure their security.
10. Assess Security Capabilities Sections
3PAOs must conduct assessments of several of the system’s technical, management, and operational capabilities via a combination of interviews, observations, demonstrations, examinations, and on-site visits. The assessment must be done based on an accurate ABD and DFD and should not rely on a CSP’s written documentation and interviews.
11. Complete Executive Summary and Ensure Alignment with Entire Document
The Executive Summary must contain a number of items, including overall alignment with the NIST definition of cloud computing and a self-service portal. This document should also note whether the CSP is pursuing a JAB P-ATO or an Agency ATO, while highlighting the CSPs strengths and weaknesses. The executive summary also asks that 3PAOs describe risks associated with interconnections and with the external systems and services that are not FedRAMP Authorized. Organizations should be sure their final Executive Summary is exact, concise, easily understood and free of any marketing content that promotes their products or services.
12. Complete Each Security Control Capability Statement to Include the 3PAO Test Methodology
To successfully complete a RAR, 3PAOs must complete each security control capability statement in every section of the RAR, and convey the capability, supporting evidence, and any missing elements. The capability cannot simply be a copy and paste from the System Security Plan (SSP) but rather a fully addressed question and then the 3PAO should indicate how they interviewed, examined, and or observed the capability in place. Throughout the security control capability statement, we suggest a 3PAOs only answer “yes” if the answer is consistently “yes.” Partially implemented areas should be answered “no” with a description of what is missing to achieve a “yes”.
A-LIGN Can Help
Does the FedRAMP certification process seem overwhelming? A-LIGN can help by making the process seamless. As a top five FedRAMP assessor, we understand the FedRAMP journey from readiness to authorization.
Get in touch with us to learn how we can guide you to authorization.
Understanding the New FedRAMP Rev 5 Baselines
At the end of last year, the Federal Risk and Authorization Management Program (FedRAMP) released a draft of their FedRAMP Revision 5 (Rev 5) baselines. Since the inception of the program in 2011, FedRAMP has used NIST (National Institute of Standards and Technology) standards and guidelines to offer standardized security requirements for cloud service providers (CSPs). As such, the forthcoming FedRAMP Rev 5 is based on NIST 800-53 Rev 5, which was released in September 2020.
Read on to discover how FedRAMP Rev 5 compares to Rev 4, next steps for the program, and other relevant FedRAMP updates.
FedRAMP Rev 4 vs. Rev 5: Introducing a threat-based methodology
The most noteworthy difference between FedRAMP Rev 4 and Rev 5 is that FedRAMP has introduced a threat-based methodology to determine which controls to add on to the established NIST 800-53 Rev 5 baselines.
Specifically, FedRAMP evaluated each NIST 800-53 Rev 5 control on its ability to protect, detect, and/or respond according to the methods outlined in the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) Framework v8.2. MITRE ATT&CK is a carefully curated, regularly updated knowledge base covering cyber threat behavior.
Benefits of FedRAMP’s new threat-based approach include:
- Enhanced security against the top threats to federal information systems
- Identification of notable gaps and duplication in security efforts
- Streamlining of the overall FedRAMP authorization process
- Increased potential for reuse of authorization packages across government agencies
Control differences in FedRAMP Rev 4 vs. Rev 5
When NIST 800-53 Rev 5 was released, NIST called it “not just a minor update but rather a complete renovation.” I’ve previously written about how this special publication introduced new control categories with a focus on outcome-based controls as well as a greater emphasis on privacy. Consequently, FedRAMP Rev 5 also provides a “proactive and systematic approach to ensuring that critical systems, components, and services are sufficiently trustworthy and have the necessary resilience to defend the economic and national security interests of the United States.”
In past revisions of FedRAMP, the number of controls required has been significant, especially for Moderate and High impact levels. However, the new threat-based methodology has minimized the amount of controls added by FedRAMP. Listed below are the number of additional controls that the FedRAMP Program Management Office (PMO) and Joint Advisory Board (JAB) have proposed in addition to the current FedRAMP baselines:
- Low Baseline — 1 additional control
- Moderate Baseline — 17 additional controls
- High Baseline — 22 additional controls
Ultimately, the strategic control selection put forward for FedRAMP Rev 5 will enable a more efficient security authorization process for all parties involved.
Next steps for FedRAMP Rev 5
The draft of the FedRAMP Rev 5 baselines is open for public comment until April 1, 2022. You can provide feedback on the proposed baselines by annotating this document and emailing it to [email protected] before the deadline.
After feedback has been collected from government entities and the federal security community, FedRAMP will review all public comments and update the Rev 5 baselines accordingly. Once these final changes have been made, FedRAMP Rev 5 will be officially published alongside related documentation, guidance, and an estimated compliance timeline.
When FedRAMP Rev 5 is released, it will include Open Security Controls Assessment Language (OSCAL) versions of the updated baselines. FedRAMP uses OSCAL to automate a large portion of security package review. CSPs and third-party assessment organizations (3PAOs) may also use OSCAL to carry out their own self-tests prior to submission. This technology ultimately results in a faster and more accurate validation and authorization process.
Additional FedRAMP updates
FedRAMP announced two important updates at the beginning of this year that I’d also like to highlight. First, the program released an updated Readiness Assessment Report (RAR) Guide and templates that are designed to provide more detailed guidance for 3PAOs in assessing CSPs. After completing a RAR, a 3PAO will attest to an organization’s readiness for the official authorization process. The new guide and templates are designed to reduce complexity and redundancy in the process, as well as provide clearer instructions based on feedback from 3PAOs and CSPs.
The second relevant piece of FedRAMP news is the publication of an updated CSP Authorization Playbook to give CSPs a more comprehensive understanding of what the authorization process entails. This updated playbook exists across two volumes: Volume I details how to prepare for FedRAMP, various paths to authorization, and items to consider prior to getting started. Volume II focuses on the development of a high-quality security package to reduce the need for revisions during the review process, including tips for delivering a coherent, digestible package.
Taking the fast track to FedRAMP
All of the new FedRAMP updates indicate that the program is taking feedback from the federal security community seriously and is actively working to make the authorization process faster and more efficient for everyone involved. That being said, it can be difficult to adapt to change, especially if you are not deeply familiar with the federal compliance space. As a result of this change, I recommend you review the Revision 5 updated controls and guidance to begin implementing any gaps identified.
Is your organization getting ready to pursue FedRAMP Authorization to Operate (ATO) status now or in the future? A-LIGN is an accredited 3PAO and one of the top FedRAMP assessors in the world based on our in-depth knowledge of federal compliance and hands-on experience helping CSPs get ready to do business with the U.S. government. Visit our website to learn more about our FedRAMP services.
15 Ways to Prevent Data Breaches in Your Organization
Are you feeling safe about your organization’s personal data because of standard security policies and procedures you have in place? Don’t be fooled by a false sense of security. Managing cyber-risk is a multi-faceted, whole-organization effort that requires implementation from the top levels down.
The cost of a data breach increased 10% in the past 12 months, the highest increase in the last seven years, according to IBM’s Security Services 2021 Cost of a Data Breach Report. With remote work greatly increasing out of necessity due to the COVID-19 pandemic, cybersecurity is more important than ever. IBM’s report found that remote work directly contributed to a $1.07 million increase in breaches. While security policies and procedures are important in protecting your data, your organization should consider one largely overlooked area of weakness- human error. Examples of human error risk factors include:
- Administrator system misconfiguration
- Not updating systems appropriately
- Not managing system patches
- Default password usage
- Default user ID usage
- Lost devices
- Misplaced devices
- Unlocked devices
- Incorrect disclosure procedures
Though this list is not exhaustive, it emphasizes the importance of cybersecurity education for management and employees, so that organizations are able to prevent data breaches caused by human error. Let’s dive into 15 ways your organization can better protect itself against human error and ultimately prevent data breaches.
Security Training & Human Resources
1. Education from the Top Down
It’s no accident that I noted education as the first tip. Individuals in management may think that because they have a seasoned IT security director at the helm, their duties regarding risk mitigation are fully out of their hands. However, ensuring that management and employees fully understand the potential cybersecurity risks innate to their organization is important in preventing risks.
The development of policies and procedures to prevent data breaches is essential, and educating employees both new and old on these policies and procedures is critical. Because the cybersecurity landscape is constantly changing, regularly educating management and employees on updated cybersecurity policies and procedures is necessary in mitigating risk. In addition, your organization should inform employees on new scams or potential new risks as they arise – for example, new phishing scams or websites with potential vulnerabilities.
2. Hire Security-Savvy Employees
Strong security starts with great personnel, which is why the hiring process is important. While individuals with experience can be beneficial to an organization, professionals who have a deep understanding of the current risk landscape can be invaluable to an organization while trying to implement security controls. When recruiting individuals, management should keep in mind that those they hire will play a paramount role in ensuring the security processes and procedures put in place will be followed.
In addition, management should be sure to maintain communication lines with their security and compliance team in order to ensure that all potential threats are being monitored carefully.
3. Develop an Exit Strategy
It’s crucial to create an exit strategy for employees that are leaving your organization. This includes changing passwords, ensuring that computers and personal devices no longer have sensitive information available on them, and developing contracts that include legal repercussion for sharing or utilizing sensitive data.
Limiting Access to Data
4. The Less Data, the Better
Since cyber criminals can only steal information that the organization has access to, one of the major ways to minimize risk is to limit data availability:
- Don’t collect information that isn’t relevant to your business.
- Reduce the number of places where data is physically stored.
- Purge data early and often.
You prevent data breaches by minimizing the amount of data your organization stores on-premises or in the cloud.
5. Zero Trust
Restrict access of resources to only the people who need them. Every time a user wants to access specific data or a specific resource, the user will need to authenticate and prove who they are.
For example, if a user needs to read the details from a document to do a portion of their job, they will only be granted privileges to read the document; they will not be able to edit or modify that document in any way.
This restriction around privileges is done intentionally. After all, a zero-trust architecture uses zero trust principles to manage workflow and is designed to assume that an internal network is already infected with various threats. This is a unique mental hurdle for many organizations since most people just assume that an internal network is protected.
6. Purge Your Data Properly
It isn’t enough to simply purge your data. Getting rid of sensitive data in the appropriate fashion is the other half of the battle.
Too often, employees think that they are getting rid of all their data when they remove files that are located on their desktop, without realizing that other clones of the files are present within the body of the computer. By teaching employees’ proper data disposal techniques, you’re able to minimize the risk of having that data get into the wrong hands.
The Impact of Remote Work
7. Monitor Your BYOD Programs
BYOD or Bring Your Own Device, is a program where employees bring their own technology (computers, tablets, cell phones, etc.) to work. Many organizations allow this type of program so that employees are able to use technology that they have a better understanding of. This reduces training time and increases productivity. Oftentimes, BYOD occurs unintentionally as more of the workforce operates remotely and has daily access to their own devices.
However, one of the major risks is that employees do not feel as though they need to be utilizing organizational policies when they are using their “personal” device. The risk here is that while the device may be used for both work and fun, sensitive data is still readily available.
In addition, these programs leave IT administrators frustrated, as they have to understand necessary updates and patches for a litany of different devices instead of just a few.
By implementing strong BYOD policies that require employees to fully understand the risks inherent with the utilization of their own devices, organizations are able to fully prevent data breaches from happening. These programs should emphasize or consider:
- Password and device-encryption requirements
- Update and patch requirements
- Lost or misplaced device notification for emergency response and remote data-wiping
- Utilization of tracking software
- Establishment of secure app workflows
- Anti-malware software
- Jailbreak prevention
- Sandboxing
- Device partitioning
The creation of appropriate BYOD management and policies allow for the program to work successfully, instead of becoming a pain point for organizations.
8. Secure Your Networks
Employees are constantly on mobile devices, and often times have their devices set to “Automatically Connect” to the closest Wi-Fi available. This leaves security professionals floundering, as there have been more than a few fake Wi-Fi capture spots that pull sensitive information from these “Hot Spots.”
Ensure the security of your network by investing in a personal or corporate VPN, that way all of the data that is being utilized is appropriately encrypted at the source.
IT’s Role in Security
9. Update Software with All Patches and Updates
Software companies are constantly updating their product in order to ensure that their devices are secure for use. Outside companies are constantly finding new vulnerabilities in their software, and patches and updates allow for organizations to ensure that these vulnerabilities do not affect their business functions. Security and IT teams should not only be aware of the latest software but execute on all patches and updates.
10. Develop “Appropriate Usage” Guidelines for Company Technology
Educate employees on the appropriate usage of organizational technology. This includes when, where and how to login to accounts, how to check their connection to ensure it is reliable and secure, and when not to use devices.
11. Hold Outside Vendors to the Same Standards
By only working with organizations with the correct security and regulatory designations, you are able to prevent data breaches by ensuring all of the appropriate controls are in place. While it may be cheaper to hire organizations that hold no designations, or function outside of governing bodies with strict regulation, it is not cheaper than the consumers that are lost due to a data breach.
Service providers will likely face an increased burden in 2022 to furnish additional attestation and certification documents to comply with each customer’s own vendor risk management programs. Some customers will request standard documentation — like the ISO 22701 certification or a SOC 2 attestation — while others may layer on custom requirements for vendors based on the specifics of their relationship and business. Service providers can also expect to spend more time reporting back to customers as they implement new processes for ongoing oversight of vendors.
At the end of the day, if your vendor makes a mistake – it is your clients on the line, not just theirs.
Preparedness & Disaster Recovery
12. Prepare for the Worst
Establishing a disaster management plan allows for your organization to feel prepared if the worst were to happen. While all of your preparations can help you to prevent data breaches, your risk is never fully mitigated. Being prepared allows your team to have a full understanding of their job in order to prevent the breach from growing, or causing unnecessary customer backlash.
A-LIGN’s Ransomware Preparedness Assessment service review the risk, security preparedness and existing controls utilizing the NIST cybersecurity framework. This assessment allows A-LIGN’s expert to identify any gaps in your organization’s cybersecurity plan, uncover cybersecurity vulnerability through penetration testing and social engineering and ensures you know how to respond if an attack occurs.
13. Test Out Your Disaster Management Plan
Put your breach protocol to the test with a mock disaster. See how well your team is prepared for a potential breach and troubleshoot problems with your protocol before it becomes a reality.
14. Audit Your Organization Regularly
By auditing your team on their practices, you are able to see where there are potential problems that could lead to future breaches. This allows your organization to modify policies and protocols prior to an issue.
15. Notify Early and Appropriately
If your team even vaguely believes that there was a potential data breach, communicate with your organization’s security management team and notify the appropriate authorities immediately.
The sooner that your team is able to respond to an incident, the greater the chance you have in being able to manage the potential damage to your organization and its clients. Reporting unusual or suspicious activity is the difference between a major breach and a minor one.
Taking Steps Toward a Fully Secure Organization
I have found that most organizations begin with a combination of VPN and multi-factor authentication, or they adopt a zero-trust architecture, but that is only the start. Every organization needs to understand its own architecture in order to identify its threat surface. Penetration testing can also help to identify and highlight some of these risks.
Ultimately, it comes down to the importance of knowing where your assets reside, and implementing the appropriate security training, policies and procedures needed to protect them.