Compliance is more than a legal necessity; it’s a way to create business value. Complying with frameworks like SOC 2 and ISO 27001 gives your organization the level of security it needs to operate effectively, establishes trust with your customers, and cultivates a culture of security within your business. Read on to learn why earning these certifications goes beyond checking a box to generate business value.
SOC 2 and ISO 27001 defined
Applicable to all industries, SOC 2 and ISO 27001 are two of the most effective cybersecurity frameworks. Pursuing a SOC 2 report or an ISO 27001 certification (or both) can help increase trust with customers, prospects, and partners.
A SOC 2 audit is performed to ensure an organization securely manages their data to protect the privacy of both the organization and its clients. This framework is used in many industries, but it’s particularly useful for software-as-a-service companies and managed service providers.
Our experts recommend proactively completing a SOC 2 audit before a customer asks to see a report. Scheduling an audit and having a report on-hand when a prospect asks for one will prevent you from delaying important deals.
ISO 27001 is used to demonstrate an organization’s commitment to a strong cybersecurity program. This international standard focuses on data confidentiality, integrity, and availability. Earning an ISO 27001 certification showcases your organization’s commitment to data protection. ISO 27001 is most often used by SaaS, cloud computing, and data processing companies.
By building a culture of information security and diligence, organizations can reduce security incidents through implemented controls that are specific to their unique risks. Customers and partners will also feel more at ease entering a deal where the organization they want to work with has proven their dedication to risk management.
The value of SOC 2 and ISO 27001
These frameworks demonstrate your organization’s commitment to security, particularly when combined. But how do they drive business value?
Build trust among customers and partners
Earning your SOC 2 or ISO 27001 certification builds trust among your customers and partners. These stakeholders want to understand the steps your organization takes to process and manage their data to ensure that it’s in good hands.
The best way to demonstrate your company’s dedication to safeguarding their valuable information is through an audit conducted by a third party. Successfully completing an audit with an outside vendor shows that your organization cares to protect its customers’ data and that your processes match this commitment.
Mitigate risk
Cybersecurity breaches are costly – averaging $4.9M in 2024, according to IBM. Plus, depending on the industry, your organization could be spending even more money to make up for a data breach.
SOC 2 and ISO 27001 help mitigate this risk by defining responsibilities and demonstrating that your organization has sophisticated, mature cybersecurity and privacy practices. Plus, a data breach doesn’t just cost money, it can cost you your reputation as a quality company. Prevent a potential cybersecurity incident by protecting your customers’ data now, before it’s too late.
Beyond SOC 2
Once seen as a strong competitive advantage, earning your SOC 2 certification is now seen as the cost of doing business. It’s a no-brainer to implement this framework that will just get you started on your compliance journey. In fact, 92% of organizations are now conducting at least two audits or assessments per year according to the 2025 Compliance Benchmark Report. This demonstrates that companies are going beyond SOC 2 in today’s regulatory landscape and pursuing additional frameworks like ISO 27001, SOC 1, HIPAA and more to show their commitment to security as an organization. ISO 27001 appears to be taking center stage for the next most important framework with ISO 27001 certifications increasing by more than 20% year over year across all companies surveyed in the 2025 Compliance Benchmark Report.
Having a SOC 2 report is the bare minimum in compliance. As organizations increasingly depend on third-party providers to handle sensitive information, having a SOC 2 report is a fundamental benchmark.
Erika Fry, Director of IT Security, Boomi
Why A-LIGN
If you’re ready to take the next step, contact A-LIGN today to begin your journey to SOC 2 or ISO 27001 compliance. A-LIGN’s commitment to a high-quality compliance strategy is demonstrated by:
- 17.5k+ SOC assessments completed
- 4K+ ISO assessments completed
- #1 SOC 2 issuer in the world
A-LIGN is the leading provider of high-quality, efficient cybersecurity compliance programs. Combining experienced auditors and audit management technology, A-LIGN provides the widest breadth and depth of services including SOC 2, ISO 27001, HITRUST, FedRAMP, and PCI. A-LIGN is the number one issuer of SOC 2 and a leading HITRUST and FedRAMP assessor.
Navigating AI Regulations Around the World
As AI continues to grow, governments around the world are stepping up to establish regulatory frameworks that ensure its ethical and responsible use. From safeguarding human rights to promoting transparency and accountability, these regulations aim to strike a balance between fostering innovation and mitigating risks.
In this blog, we’ll explore key AI regulations from different regions, highlighting their objectives, approaches, and the impact they aim to achieve. We’ll keep this resource updated as new regulations are introduced, so bookmark this page as your go-to guide.
United States
The United States is taking a state-driven and federal approach to AI regulation, with laws focusing on transparency, accountability, and consumer protection. Here are some key regulations shaping AI governance in the U.S.:
California’s Generative AI Training Data Transparency Act (AB 2013)
California’s AB 2013 is the first U.S. law to mandate transparency in generative AI training data. It aims to enhance accountability, protect personal information, and provide users with greater insight into how AI outputs are generated. Signed in September 2024 and scheduled to take effect January 1, 2026, this law requires developers to publicly disclose detailed information about the datasets used to train their AI systems.
Colorado Senate Bill 24-205: Consumer Protections for AI
Colorado’s Senate Bill 24-205 aims to protect residents from algorithmic discrimination in high-risk AI systems. Passed in May 2024 and set to take effect on February 1, 2026, the law prioritizes transparency, risk management, and fairness in critical areas such as employment, housing, and finance. By assigning clear responsibilities to developers and deployers, it ensures AI systems are used ethically and without bias in decisions that significantly impact individuals’ lives.
Texas Responsible AI Governance Act (TRAIGA)
Signed in June 2025 and scheduled to take effect on January 1, 2026, TRAIGA establishes a regulatory framework for AI systems in Texas. The legislation focuses on transparency, risk management, and consumer protection, particularly for high-risk AI systems. It also includes a regulatory sandbox to encourage innovation while ensuring responsible AI development and deployment.
US Artificial Intelligence Research, Innovation, and Accountability Act (S. 3312)
This proposed U.S. legislation introduces compliance requirements for generative AI, high-impact, and critical-impact systems. It aims to enhance transparency, accountability, and risk management while fostering innovation. Although not enacted, the bill reflects a growing push for structured AI governance, particularly in applications that affect public trust, safety, and individual rights.
Europe
Europe is setting the standard for AI governance worldwide with its risk-based approach. Below are some of the region’s most influential regulations:
The EU AI Act
The EU AI Act is a landmark framework for regulating artificial intelligence globally. It introduces a risk-based classification system, categorizing AI applications into four levels: unacceptable, high, limited, and minimal risk. Each category is subject to specific rules and restrictions, requiring companies operating in the EU to implement compliance measures to mitigate legal and operational risks. Initially proposed in April 2021, the EU AI Act underwent final approval in 2024, with certain provisions becoming enforceable in 2025.
Council of Europe Framework Convention on AI, Human Rights, Democracy, and the Rule of Law
This Framework Convention establishes a comprehensive legal framework to ensure AI activities respect fundamental human rights, democratic principles, and the rule of law. It addresses risks such as discrimination, privacy breaches, and threats to democratic processes. This applies to public authorities and private entities acting on their behalf, mandating context-specific measures to manage AI-related risks effectively. Signed in September 2024, its adoption is ongoing, with implementation timelines varying across member states as they finalize national commitments.
Other regions
Across the globe, countries are introducing AI regulations that reflect their priorities and challenges. Here’s what’s happening in other regions around the world:
Brazil’s AI Bill (PL 2338/2023)
Brazil’s AI Bill aims to create a robust framework for the ethical and responsible development, deployment, and use of AI systems. It adopts a risk-based approach, imposing stricter regulations on high-risk systems that could impact public safety or fundamental rights. This bill emphasizes transparency, fairness, and alignment with Brazil’s General Data Protection Law (LGPD) to safeguard privacy. It also proposes the establishment of a regulatory authority to oversee compliance and promote innovation. Approve by the Senate in December 2024, the bill is still under legislative review, but its core measures are projected to take effect in 2026.
South Korea’s Basic Act on AI Advancement and Trust
South Korea’s Basic Act on AI establishes a regulatory framework to promote responsible AI development while maintaining public trust. The Basic Act, enacted in January 2025 and scheduled to take effect on January 22, 2026, emphasizes safety, transparency, and fairness, particularly for high-impact and generative AI systems. It also introduces initiatives such as a national AI control tower, an AI safety institute, and support for R&D, data infrastructure, and talent development.
Japan’s Act on Promotion of Research and Development and Utilization of Artificial Intelligence-Related Technologies (The “AI Bill”)
Japan’s AI Bill is the country’s first law explicitly regulating artificial intelligence. Enacted in May 2025 and taking effect almost immediately, this bill outlines core principles for AI research, development, and use, while establishing the government’s Fundamental Plan for AI. The legislation also creates an Artificial Intelligence Strategy Center to oversee national policies and promote ethical AI practices.
Building a future of ethical AI
As artificial intelligence continues to reshape industries and societies, the global regulatory landscape is evolving to ensure its ethical and responsible use. By understanding and navigating these frameworks, businesses and stakeholders can not only mitigate risks but also unlock AI’s full potential to drive innovation.
How to Successfully Prepare for an Audit
Preparing for your next audit is just as important as the audit itself. Whether it’s an audit for SOC 2, ISO 27001, or another framework, this process involves gathering documentation, understanding new frameworks, and ensuring your organization is set up for success. There are many ways to accomplish your audit preparation including readiness tools, consultants, and more. Keep reading to explore these audit preparation methods and decide which is the best fit for your organization.
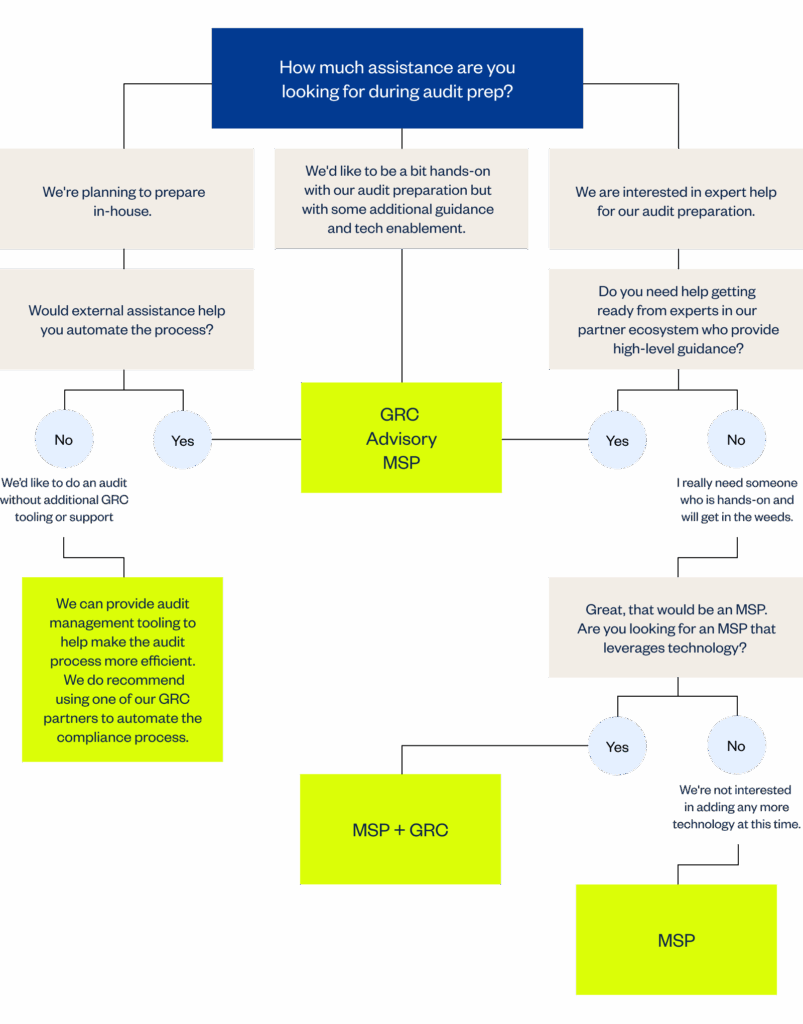
Types of readiness partners
There are three primary types of readiness partners, or the option to rely on internal resources to ensure proper readiness. These are all great options for succeeding on your journey to compliance, the trick is selecting the right fit for your organization’s needs.
vCISOs
Virtual CISOs, often referred to as vCISOs, serve as the designated security leader for your organization. These roles operate as a CISO without being a direct employee of your company. This person is empowered to make strategic decisions, authorize purchases, and act on your behalf in the interest of cybersecurity and risk management. Typically, a vCISO is leveraged in companies that do not have a full-time information security leader, like a CISO, that can provide support for compliance and information security initiatives.
MSPs
Managed service providers are third-party companies that operate as an extension of your internal team, overseeing the deployment, configuration, and management of your security and compliance technology ecosystem.
This type of partner is embedded in day-to-day operations at your company. They will handle tactical execution, integrations, and troubleshooting.
Consultant/advisory
Consultants are third-party experts that provide a high level of guidance and influence key security and compliance decisions based on deep domain expertise. These partners are often brought in to help your company navigate complex challenges, drive transformation, or steer critical security initiatives. In addition to managing the audit process, consultants can build templates that are customized to the audit requirements of an organization’s compliance strategy and ensure their customer is audit-ready.
Consultants are not directly responsible for execution, but they can play a critical role in shaping cybersecurity strategy and aligning initiatives with business objectives.
In-house preparation
You can also be your own “partner.” Some teams have the appropriate resources in-house or have a teammate with a unique skillset for audit prep. If you’d prefer not to leverage a GRC tool, you can use an audit management platform like A-SCEND, A-LIGN’s in-house tool that keeps track of documentation if you’re completing the rest of the process in-house.
Which tactic is right for you?
After you’ve evaluated all the audit preparation methods, you will need to decide which audit preparation path is right for your organization. Before making any decision, there are a few factors to keep in mind. Consider:
- Experience: How much experience do you or your teammates have with preparing for this particular kind of audit? Have you done it a million times for multiple kinds of companies? Or, is this your first time? Experience will determine how much support you will need throughout the process.
- Time: How much time does your team have available to spend preparing for your audit? Is your team lean or built out? A team with limited resources might be more likely to contract out prep work like this whereas one with a lot of bandwidth might take on this project themselves.
- Environment: Consider the type of environment you are having audited. Is it more complex or simple? Even the most experienced compliance professional might not know enough about working in your kind of environment to take on audit prep.
- Budget: Your budget is going to determine the options available to you. If you have a limited budget, consider whether you will need a tool to help automate the process. If so, a GRC tool would be a great option. If your budget can’t accommodate another tool, you can leverage an audit management system. For those with more budget at their disposal, expert assistance throughout the process with a consultant is a great option.
Why engage with A-LIGN early
Before choosing your path, engage with a trusted compliance auditor like A-LIGN that can provide high-quality audits with an expansive network of partners that include GRC tools, MSP providers and consultants to ensure you’re ready for your next audit.
A-LIGN can help connect you with the right GRC tools and trusted consultants to set you up for success and streamline the audit process. Existing relationships can simplify the process for preparation and your audit cycle. Plus, our auditors can provide perspective on GRC tools and best ways of working to save time during the evidence collection process.
If you choose the in-house route for preparation, our audit management platform, A-SCEND, can simplify the process and give your team peace of mind that your preparation is well documented.
Our responsibility as a quality audit partner is to provide a high-quality experience and ensure our clients receive expert guidance. Ready to simplify your audit cycle? Contact A-LIGN today.
What Lockheed Martin’s CMMC Announcement Means for Subcontractors
Lockheed Martin, a global leader in defense and aerospace innovation, issued a decisive update regarding its implementation of Cybersecurity Maturity Model Certification (CMMC) requirements. This announcement underscores a critical trend sweeping the defense industry — an increasing push by Department of Defense (DoD) prime contractors to elevate and enforce stringent cybersecurity standards among their subcontractors.
If you’re a business working with or aspiring to work with DoD contractors, you might already feel the pressure of meeting compliance benchmarks. However, this is more than just fine print in a contract: CMMC compliance is now a non-negotiable gateway to participating in defense supply chains.
The bigger picture: Prime contractors raising the bar
For years, cyber threats have escalated in sophistication and frequency, threatening national security and the integrity of the defense supply chain. Recognizing the stakes, the DoD launched CMMC as a way to standardize cybersecurity practices across all organizations working with sensitive federal information.
Prime contractors like Lockheed Martin are tasked with ensuring their entire network of subcontractors and suppliers meets these strict cybersecurity requirements as single gap in compliance anywhere along the supply chain could lead to devastating security breaches. This strategic shift by primes not only secures their operations but also reflects the DoD’s unwavering commitment to safeguarding controlled unclassified information (CUI).
By tightening requirements, prime contractors are signaling that every link in the chain must be fortified. Subcontractors, especially smaller firms with fewer resources, are now facing a unique and urgent challenge to align with these standards or risk their place in the defense ecosystem.
Why the urgency?
The DoD is implementing CMMC requirements incrementally, but new updates like Lockheed Martin’s announcement make one thing crystal clear: the time to act is now. Compliance is no longer optional, and waiting until deadlines are looming can result in significant setbacks.
Failing to become compliant could leave your organization at risk of losing critical contracts, disrupting your business operations, and even tarnishing your reputation. Additionally, as primes adopt these standards, organizations without a strategic compliance plan will find themselves left behind in favor of those already meeting or exceeding requirements.
Timely adoption of CMMC compliance offers exciting opportunities as well. Compliant businesses strengthen their credibility, appeal to risk-averse primes, and position themselves as leaders within the defense community. By acting on CMMC now, you’re creating a robust foundation for long-term success.
Steps to get started with CMMC
Understanding where to begin your CMMC compliance journey can feel overwhelming, but breaking it down into actionable steps can simplify the process. Here’s how your organization can tackle CMMC today:
Understand
Read the CMMC final rule, understand program requirements, review DoD’s resources, and familiarize yourself with the practices outlined in the model for each of the CMMC levels.
Identify
Identify your CMMC level and the assets in scope for your CMMC assessment. As a part of this step, you should also complete a gap assessment to identify any areas where there are gaps in your compliance.
Prepare
Develop an implementation plan to address vulnerabilities found in the gap assessment. Prepare for the C3PAO assessment by gathering evidence and preparing for interview questions. During this stage, you may want to undergo a mock audit.
Assess
Following the CyberAB’s CMMC Assessment Process, the C3PAO will review documentation and complete interviews with your team before putting together the final report. If you’ve done the appropriate pre-work, gap assessments, and mock assessments, your team should be well prepared for this step in the process.
Improve
After receiving your certification, the work continues. Plan for continuous improvement and ensure you understand the next steps for future assessments.
A-LIGN’s role in CMMC compliance
Navigating compliance on your own can be complex, but partnering with experts like A-LIGN can streamline your roadmap to success. As a top C3PAO with over 20 years of experience, A-LIGN has completed over 1,000 NIST-based assessments, including FedRAMP, GovRAMP, NIST 800-171. Our trusted team of experts equips businesses with the tools, training, and guidance needed to confidently achieve compliance and securely scale their operations.
By collaborating with a trusted advisor, you not only save time and resources but gain peace of mind knowing you’re meeting prime contractor expectations and DoD mandates.
Act today or be left behind
Lockheed Martin’s latest announcement isn’t just another update, it represents an inflection point for subcontractors across the defense industry. The window to prepare for CMMC compliance is closing, and organizations that proactively align with these standards now will have a competitive advantage.
Don’t wait until it’s too late. Start preparing for CMMC today. Strengthen your cybersecurity posture, secure future business opportunities, and ensure your place in a resilient supply chain that safeguards America’s security.
CMMC Phase 1: Why Contractors Shouldn’t Bet Everything on Self-Attestation
As CMMC enters its official rollout, many defense contractors are treating Phase 1 as a 12-month grace period — a window where self-attestation will be the only requirement for compliance with Level 2. And while that’s technically what the baseline rule allows, there’s a critical detail many are missing:
DoD contracting officers have discretion to require third-party CMMC certifications — even during Phase 1.
This is explicitly stated in the 32 CFR rule, but many organizations are moving forward as if self-attestation is guaranteed. Here’s why that’s a risky assumption — and how you can prepare accordingly.
The costly misconception about CMMC timing
Here’s where many companies are getting it wrong. A common belief is that CMMC certification isn’t needed until 12 months after 48 CFR becomes effective on November 10, 2025. While this phased rollout timeline applies in general, an important detail tucked into the 32 CFR CMMC Program Rule states that DoD Program Managers will have discretion over requiring Level 2 CMMC Certification — even during the first 12 months.
Yes, you read that right. According to the rule:
“Phase 1. DoD intends to include the requirement for CMMC Statuses of Level 1 (Self) or Level 2 (Self)… DoD may also, at its discretion, include the requirement for CMMC Status of Level 2 (C3PAO) in place of the Level 2 (Self) CMMC Status for applicable DoD solicitations and contracts.”
(Source: 32 CFR Part 170.3 e (1) – Cybersecurity Maturity Model Certification (CMMC) Program Rule)
That final sentence is the most important — and often overlooked.
Key takeaway:
If your CMMC strategy revolves around hoping DoD Program Managers won’t enforce certification requirements early, you’re taking significant risks with your pipeline.
What this means in practice
Here’s what’s happening on the ground:
- Many primes are already flowing down CMMC certification requirements to their subs, regardless of phase.
- We’ve seen early RFIs and RFPs include CMMC language — including third-party certification expectations.
- DoD contract officers could require CMMC Level 2 Certifications immediately 48 CFR’s effective date of November 10. Now, readiness is no longer optional and all new DoD solicitations and contracts include some level of CMMC requirement.
Bottom line: the rules may allow for self-attestation, but your contract may not.
The risk of misreading Phase 1
Contractors who assume that Phase 1 guarantees a 12-month reprieve from C3PAO involvement are setting themselves up for:
- Contract risks: Organizations risk bid disqualification due to lack of a required third-party certification.
- Competitive disadvantage: Proactive competitors will be certified and ready to go. Delaying your own certification gives them the edge to secure more opportunities you could have been eligible for.
- Cost surges: The longer you wait, the higher the demand for certification services will be. This could lead to inflated service costs and fewer available resources as deadlines get closer.
- Lost trust: Primes and customers can lose trust, knowing that a contract’s status was unable to be awarded due to your lack of preparedness when the requirements come.
How contractors can prepare
Proactive organizations are avoiding the “wait and see” mindset. Here’s what we recommend:
- Understand: Read the program requirements and familiarize yourself with the practices outlined in the model for each of the CMMC levels.
- Identify: Based on your level, you must identify your scope and any gaps in compliance.
- Prepare: Develop an implementation plan and prepare for the C3PAO assessment.
- Assess: Your C3PAO will complete the CMMC assessment for certification.
- Improve: Perform annual self-assessments before renewing your 3-year CMMC certification.
Learn more: Understand what the guidance means for you, what to look for in a C3PAO, and prepare for your assessment with our CMMC Buyer’s Guide.
Final word
Phase 1 of CMMC’s rollout is not a blanket exemption from certification. It’s a flexible phase that gives the DoD — and contracting officers — room to assess risk and require certification when they see fit.
Don’t leave your compliance future up to chance. By taking action now, you’re not only protecting your pipeline but also safeguarding your reputation as a trusted partner in the defense supply chain.
Need help navigating your CMMC strategy? Schedule a consultation with our team of experts and ensure your organization is equipped to succeed.
Guide: How to Transfer ISO Certification Bodies
Your compliance team dedicates time and mental energy toward securing the best quality ISO certifications to keep your organization in good standing. But things don’t always work out with your certification body. Keep reading to learn about the process of transferring your company’s ISO certificates to a new auditor.
Why would you transfer your ISO certificate?
There are a number of reasons you may want to change your current auditor:
- Inefficient audit process
- Poor communication
- Unsatisfactory final report and certificate
- Consolidating your audit cycles
If any of these sound familiar, you may be heading towards making the decision to finding a new audit partner. But it doesn’t have to be overwhelming. The right partner will make it all worth your while.
Who is eligible to transfer their certificate?
While you might think the answer to this is anyone – it’s not. There are a few criteria that should be met before committing to a certificate transfer:
- Accredited certification body: If you’re looking to transfer to an accredited auditor, your certificate must be from an accredited certification body with valid accredited standards.
- Enough time: This process may take a few weeks to collect the documentation and coordinate with the prior certification body. Pay attention to the timeline for required surveillance audits so that you don’t allow your certificate to suspend of expire. Plan ahead so you have plenty of time for the transfer.
- Certificate scope: Transferring your certificate doesn’t mean you get to expand the scope or locations of your audit, it must stay the same or be a reduced scope for you to move from one auditor to another. You can add more locations or additional scope in your next audit cycle.
What is the process for transferring ISO certificates?
The process for transferring your ISO certificate can be tedious, but the right audit partner will simplify the transition. Take the time to understand what documents you should prepare and how to navigate the steps to transfer auditors to reduce stress and streamline the process.
Preparation
It should come as no surprise that you will need to gather documents before transferring auditors. First, it’s imperative that you verify the validity of your certificate. You cannot transfer certificates from an unaccredited certification body to an accredited one. Luckily, the International Accreditation Forum (IAF) makes it easy to verify the accreditation of your CB with their database – IAF CertSearch. If you worked with an unaccredited certification body, you’ll need to complete an initial certification audit with an accredited certification body.
After this step is complete, we recommend checking the expiration date and scope of your ISO certification. If your certification is days or weeks from expiring, now is likely not the time to begin the transfer process. In addition, you should understand that the scope of your audit must stay the same or reduced for the transfer process. A new location or expanded scope may be added after the certificate has been transferred, either during the next audit or as a special audit.
You should ensure you start this process at least three months before your certificate is at risk of being suspended due to surveillance audits not meeting the required timeline or your certificate expires, preferably more. This is because the process of approving a transfer once you’ve chosen a new certification body can take several weeks. Then, you’ll need to get on the schedule for your next audit. When transferring auditors, it’s particularly important to not rush the process and do it right.
Transfer Process
Now that you’ve prepared and verified your certificate, it’s time to get started!
This step in the process will be very similar to the last time you did it: you will research certification bodies and look for one that aligns with your priorities. We recommend choosing a partner that has an experienced audit team, a high standard of quality, and prioritizes efficiency through technology and audit consolidation. For a comprehensive checklist of questions to ask potential CBs, check out our ISO 27001 Buyer’s Guide.
Checklist: Questions to ask an assessor
- What is your experience with ISO certification audits?
- Does your team have experience with multiple ISO certification standards including ISO/IEC 27001, ISO/IEC 42001 or ISO/IEC 27701?
- Does your organization conduct other audits such as SOC 2, PCI DSS or HITRUST?
- What can I expect during the audit process?
- How do you ensure the quality of your audits?
- How much will my audit cost?
- How long does an ISO audit take with your organization?
- Do you have references and case studies from satisfied customers?
For the complete checklist, download our ISO 27001 Buyer’s Guide.
Your commitment
You’ve chosen a new certification body that aligns with your organization’s priorities – congratulations! Here’s what the process will look like at this stage:
- Certificate verification: At this time, you will provide your current certificate to your new certification body’s audit team. They will verify its validity and request a transfer from your former CB. This step could take some time, so be prepared to wait.
- Review of information: In order to transfer your certificate to a new certification body, a number of items will need to be reviewed in accordance with IAF MD 2: IAF Mandatory Document for the Transfer of Accredited Certification of Management Systems. Your CB will review confirmation of the AB and CB scopes, reasons for transfer, sites that are transferring, previous reports, certificates, audit program, complaints received and additional audits with regulatory bodies. Additionally, your new certification will need to coordinate with the previous certification body to ensure all nonconformities have verified actions in accordance with the severity and that the status of the certificate is not in danger of falling out of active status.
- Contract signing: While a contract may be signed prior to a transfer, an amendment will need to be executed if the transfer is not accepted by the certification body.
Acceptance
After your former certification body accepts the transfer, your new certification body will issue you an updated certificate on the new CB’s paper. There will be no lapse in coverage if your certificate was valid and the scope is the same. Your ISO certification will now continue through the audit lifecycle.
If the certification body does not accept the transfer, you will need to start with an initial certification audit.
Best practices for transferring ISO certificates
- Start early: Like we mentioned, give yourself at least three months from the time you choose your new CB to the expiration date of your certificate. You don’t want any lapse in coverage or to have to start the audit process over again!
- Ensure the validity of your certificate: IAF makes it easy to check the validity of your certification body. Simply look up your CBs information in their database to confirm accreditation.
- Choose a quality partner: You’ve seen the results of choosing the wrong partner. Take the time to choose a partner that meets your standards of quality and aligns with your values in the process.
- Now is the time to streamline: Pick a provider that can handle all of your audits and highlight overlaps you didn’t even know existed. This will help your team work smarter, not harder.
If you’re ready to work with a high-quality audit partner that prioritizes team expertise, technology, and efficiency, A-LIGN may be the choice for you. Contact us today to learn how to get started on the path to a first-class final report.
The European Union Artificial Intelligence Act is a framework developed by the EU to regulate artificial intelligence development and use. This piece of legislation is relatively new, but its phased approach means companies must take action now. If you’re not sure where to begin with the EU AI Act, read on for our guide to this emerging standard and next steps for becoming compliant.
What is the EU AI Act and why is it important?
The EU AI Act is one of the first comprehensive frameworks for regulating AI globally. It defines a risk-based AI classification system and requires companies doing business in the EU to proactively implement compliance measures to avoid legal and operational risks. The act classifies AI applications into four risk categories: unacceptable, high, limited, and minimal, each subject to specific rules or restrictions.
Who does the EU AI Act apply to?
The EU AI Act is far-reaching. This standard applies to:
- Organizations placing an AI product on the market in the EU
- Users of AI products and services in the EU
- Providers or users of an AI system intended to be used in the EU
It’s important to note that the EU AI Act isn’t just for organizations or users based in the EU, but also any organization working, selling, or using AI products in the EU.
What are the risk categories defined by the EU AI Act?
The EU AI Act organizes AI products and uses into four risk categories: unacceptable, high risk, limited risk, and minimal risk.
Unacceptable risk
This is the most severe level of risk defined by the EU AI Act. According to the European Parliament, the EU AI Act highlights several banned AI applications in the EU including:
- Cognitive behavioral manipulation of people or specific vulnerable groups. This includes things like voice-activated toys that could encourage dangerous behavior in children
- Social scoring AI: classifying people based on behavior, socio-economic status or personal characteristics
- Biometric identification and categorization of people
- Real-time and remote biometric identification systems, such as facial recognition in public spaces
High risk
This standard considers AI systems that negatively impact safety or fundamental rights as high risk. From there, it breaks these systems into two categories:
- AI systems used in products defined by the EU’s product safety legislation like toys, aviation, card, medical devices, and lifts
- AI systems that fall into specific area that will have to be registered in an EU database, like education, law enforcement, critical infrastructure, and other related areas.
Limited risk
Some AI products and use cases will fall into this category and be subject to transparency requirements. One example of this is ChatGPT. Systems that fall into the limited risk category will need to:
- Disclose that its content was generated by AI
- Design the model to prevent it from generating illegal content
- Publish summaries of copyrighted data used for training
Minimal or no risk
Most AI systems will fall into the minimal or no risk category, meaning they have no further legal obligations.
What is the timeline for compliance?
The EU AI Act became legally binding on August 1, 2024. However, the requirements in the act will begin to take effect gradually over time with a phased roll out. Key milestones include:
- February 2, 2025: Prohibitions on certain AI systems and requirements on AI literacy start to apply.
- August 2, 2025: Rules start to apply for notified bodies, GPAI models, governance, confidentiality and penalties.
- August 2, 2026: The remainder of the AI Act starts to apply, except for some high-risk AI systems with specific qualifications.
- August 2, 2027: All systems, without exception, must meet obligations of the AI Act.
What are the penalties for noncompliance?
According to Article 99 of the EU AI Act, the penalties for noncompliance with the prohibition of the AI practices referred to in Article 5 will be subject to administrative fines of up to EUR 35,000,000, or up to 7% of worldwide annual turnover, whichever is higher.
Noncompliance with any other provisions not laid out in Article 5 will be subject to fines up to EUR 15,000,000 or up to 3% of worldwide annual turnover, whichever is higher.
The EU AI Act also sets fines for those who supply incomplete, incorrect, or misleading information to notified bodies or national competent authorities when they request information. Those fines can be up to EUR 7,500,000 or up to 1% of worldwide annual turnover, whichever is higher.
Why ISO 42001 is essential for EU AI Act compliance
This standard mandates an ongoing governance framework for AI risk management, transparency, and compliance. Unlike one-time risk assessments or ad hoc governance policies, ISO 42001 establishes a systematic, repeatable process for AI compliance, ensuring organizations:
- Proactively manage AI risks rather than responding to enforcement actions.
- Align AI governance with business operations using structured risk-management frameworks.
- Demonstrate compliance through audit-ready documentation and performance evaluation.
ISO 42001 provides an adaptable compliance framework that evolves alongside regulatory requirements, making it an ideal foundation for AI governance. Though it is not an approved harmonized standard for AI Act conformity, it does provide the foundation you’ll need to be successful when the final QMS conformity standard is released.
Next steps
Companies seeking compliance with the EU AI Act need to act now to avoid penalties and stay ahead of the curve. Enforcement will only intensify over the next two years.
We recommend reaching out to a high-quality auditor that can help your organization become compliant with the EU AI Act before it’s too late. Organizations that take action now will be best positioned to thrive in the new AI regulatory environment.
Reach out to A-LIGN today to learn how our team can get your organization on the path to compliance.
What is FedRAMP 20x?
The federal cloud landscape is transforming, thanks to FedRAMP 20x. Announced in March 2025, this pilot initiative aims to accelerate the path to FedRAMP authorization, cutting timelines from years to weeks. By simplifying processes and leveraging automation, FedRAMP 20x offers a streamlined, cloud-native approach to security compliance.
FedRAMP 20x
FedRAMP 20x addresses long-standing challenges in the FedRAMP authorization process. Traditionally, approval took years, requiring extensive documentation and layers of review. FedRAMP 20x aims to simplify this process, approving cloud services in weeks.
Key improvements include:
- Automation of compliance: Using machine-readable processes to reduce manual tasks.
- Adoption of industry standards: Aligning with frameworks like SOC 2 and ISO 27001 to leverage existing security investments.
- Continuous monitoring: Validating security through real-time data instead of periodic audits.
- Direct collaboration: Encouraging more agile relationships between Cloud Service Providers (CSPs) and federal agencies.
- Rapid innovation: Eliminating delays to enable faster adoption of secure cloud services.
This initiative prioritizes flexibility, empowering CSPs and agencies to work more directly and limit bureaucratic bottlenecks.
Phase 1 pilot program overview
Phase 1 represents a crucial testing ground for FedRAMP 20x, showcasing how streamlined processes and automation can revolutionize cloud compliance for the federal space.
Quick milestones
The first phase of FedRAMP 20x focuses on low-impact cloud systems. Open to any CSP, it replaces the traditional 325-item control baseline with a list of Key Security Indicators (KSIs). Participants submit machine-readable security documents, assessed by a Third Party Assessment Organization (3PAO). Successful systems can achieve provisional authorization in weeks.
- Timeline: Formal submissions started May 30, 2025.
- Fast-track approvals: CSPs earning low-impact authorization may gain priority for FedRAMP Moderate authorizations in the next phase.
Participation criteria
Providers suited for Phase 1 typically:
- Host solutions on FedRAMP-authorized platforms.
- Offer simple, internet-facing services.
- Maintain strong security through frameworks like SOC 2 or recent federal ATOs.
- Partner with a FedRAMP-accredited 3PAO for assessments.
The removal of the federal sponsorship requirement for low-impact systems widens access, making compliance achievable for emerging providers and small businesses.
Benefits of FedRAMP 20x
For CSPs targeting the federal market, FedRAMP 20x offers major benefits:
- Faster approvals: Reduce authorization timelines from years to weeks.
- Easier processes: Minimized paperwork and increased automation lower costs and effort.
- Self-initiation: No agency sponsor needed for low-impact systems, opening opportunities for smaller providers.
- Cloud-native alignment: Requirements are more developer-friendly, focusing on agility and outcomes.
- Encouraged innovation: Continuous monitoring ensures new features can roll out quickly without delaying compliance.
By lowering barriers and fostering competition, FedRAMP 20x brings more providers into the federal sector, supporting rapid technological advancement.
Getting ready for FedRAMP 20x
To get ready for FedRAMP 20x, CSPs should take these steps:
- Learn the new standards: Study the draft KSIs to understand security expectations.
- Assess readiness: Compare your current compliance posture to the pilot’s criteria, identifying gaps.
- Engage with stakeholders: Join FedRAMP working groups for updates and insights.
- Prepare evidence: Plan machine-readable security submissions, working closely with a 3PAO to streamline assessments.
- Maintain basics: Continue following FedRAMP Rev.5 guidelines, as traditional routes to authorization remain valid.
Organizations meeting Phase 1 criteria should consider joining the pilot to gain early access and a competitive edge. Even if you delay participation, investing in automation and compliance improvements now will prepare you for FedRAMP 20x expansion to higher-impact systems.
How A-LIGN can support your FedRAMP journey
Navigating FedRAMP alone can be challenging. A-LIGN, as a trusted FedRAMP-accredited 3PAO, offers expert guidance for traditional FedRAMP and the 20x pilot.
- Readiness assessment: We help identify gaps, align security controls, and prepare your team for FedRAMP requirements.
- Assessment and documentation: Our expertise ensures seamless evaluations, minimizing surprises during the submission process.
- Continuous monitoring: A-LIGN supports post-authorization security through ongoing assessments and adaptable strategies.
With FedRAMP 20x reshaping compliance standards, having a knowledgeable partner can make all the difference. We’re committed to supporting you at every stage, from preparation to long-term success.
Red Teaming Explained
Cyber threats are becoming more sophisticated by the day. For organizations serious about fortifying their defenses, “red teaming” has become an indispensable practice. But what exactly is red teaming, and why does it hold such an important place in modern cybersecurity strategies?
In this guide, we’ll break down the concept of red teaming, walk you through its process, explain how it differs from penetration testing, and outline its benefits.
What is red teaming?
Red teaming is a process used to simulate an adversary’s attack on a system, organization, or network to test its security, resilience, and response capabilities. The “Red Team” is a group of experts who take on the role of an attacker or adversary, attempting to exploit vulnerabilities and identify weaknesses across people, processes, and technologies of an organization.
Unlike routine security checks, red teaming is a holistic exercise. It evaluates not just technological vulnerabilities but also human and procedural gaps, offering a more comprehensive view of an organization’s readiness. It mimics real-world scenarios, forcing organizations to test their detection, response, and prevention mechanisms under controlled conditions.
When should you use red teaming?
Red teaming is especially valuable for organizations that:
- Handle sensitive customer data or intellectual property.
- Operate in highly regulated industries, like finance or healthcare.
- Desire to conduct an advanced security assessment beyond standard penetration testing.
What is the process of a Red Team exercise?
Red Team exercises are methodical, typically following these six key steps to simulate an attack and assess an organization’s weaknesses:
1. Define objectives & scope
Before launching an exercise, it’s critical to establish clear goals and identify boundaries—such as systems, people, or processes—while conducting extensive research to gather information about the target systems, organization, and personnel.
2. Planning & strategy
The Red Team begins by developing a detailed plan outlining the methods, tools, and tactics to be used during the red teaming exercise. This step ensures alignment with the agreed scope and objectives.
3. Attack simulation
Once potential weaknesses are identified, the Red Team attempts to exploit vulnerabilities using the tactics, techniques, and procedures (TTPs) of real-world adversaries. After gaining initial access, they will maintain persistence and navigate through the network to achieve defined goals, such as accessing sensitive data or critical systems.
4. Reporting & documentation
Following the exercise, a comprehensive report is created detailing TTPs, how vulnerabilities were identified, and actionable recommendations to enhance security controls.
5. Recommendations
The Red Team will then provide actionable recommendations to mitigate identified risks and strengthen the organization’s defenses.
6. Post-engagement debrief
The last step in the process is to conduct a thorough review of the exercise with stakeholders, highlighting lessons learned and discussing the implementation of mitigation strategies.
How is red teaming different from penetration testing?
Although both focus on ensuring organizations are protected against cybersecurity threats, the two services play different roles.
Penetration testing focuses on identifying and exploiting specific vulnerabilities within a defined scope. It simulates attacks to evaluate the security of specific systems, networks, or applications.
Red teaming, however, takes a more comprehensive approach. It simulates real-world cyberattacks to assess an organization’s overall security posture. These engagements use multiple TTPs to replicate the methods of advanced adversaries.
What are the benefits of red teaming?
Red teaming offers significant benefits for organizations serious about cybersecurity:
- Proactively identify and resolve risk
Red teaming goes beyond basic assessments to uncover critical vulnerabilities and provide deeper insight into your organization’s unique systems, culture, and weaknesses. This proactive approach helps identify and resolve potential risks before they can be exploited, protecting your organization from costly breaches and disruptions.
- Deeper security alignment with industry standards
Effective internal red team exercises aren’t just about fixing vulnerabilities. They also ensure your security strategies align with industry standards and regulatory requirements, particularly those set by frameworks like FedRAMP and ISO 27001. Achieving compliance with FedRAMP Rev 5 requirements is simplified through a proven, ironclad process that ensures success.
- Enhanced incident response
Conducting regular red team exercises sharpens incident response capabilities. It creates realistic, high-pressure scenarios where teams can practice detecting and mitigating threats, building stronger, more agile response capabilities over time.
- Comprehensive security evaluation
Unlike traditional vulnerability scans, red teaming evaluates your organization holistically. It goes beyond technical defenses to assess workflows and overall readiness to handle sophisticated threats.
Red teaming is the future of proactive cyber defense
As cyber threats grow more sophisticated, so must an organization’s defenses. Red teaming helps security professionals and IT managers go beyond checkbox compliance to truly assess and improve their resilience to attacks. By simulating real-world scenarios, red teaming provides a 360-degree view of security posture.
Want to take your cybersecurity to the next level? Our certified Red Teamers are equipped with the deep knowledge and credentials. With a track record of zero rejections and seamless acceptance, we ensure your red teaming exercise is compliant, efficient, and delivers without delays. Contact us today to get started.




